
bigdaddycvk
-
Content Count
9 -
Joined
-
Last visited
Content Type
Profiles
Forums
Calendar
Posts posted by bigdaddycvk
-
-
I can not get back onto the kapersky site, as my power went our during download. It states that the license expired.
The mbam log is as follows....
Malwarebytes' Anti-Malware 1.46
www.malwarebytes.org
Database version: 5103
Windows 5.1.2600 Service Pack 3
Internet Explorer 8.0.6001.18702
11/12/2010 6:17:07 PM
mbam-log-2010-11-12 (18-17-07).txt
Scan type: Quick scan
Objects scanned: 151152
Time elapsed: 26 minute(s), 7 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 0
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
(No malicious items detected)
Download TFC to your desktop
- Open the file and close any other windows.
- It will close all programs itself when run, make sure to let it run uninterrupted.
- Click the Start button to begin the process. The program should not take long to finish its job
- Once its finished it should reboot your machine, if not, do this yourself to ensure a complete clean
Please download Malwarebytes' Anti-Malware from Here
Double Click mbam-setup.exe to install the application.
- Make sure a checkmark is placed next to Update Malwarebytes' Anti-Malware and Launch Malwarebytes' Anti-Malware, then click Finish.
- If an update is found, it will download and install the latest version.
- Once the program has loaded, select "Perform Quick Scan", then click Scan.
- The scan may take some time to finish,so please be patient.
- When the scan is complete, click OK, then Show Results to view the results.
- Make sure that everything is checked, and click Remove Selected.
- When disinfection is completed, a log will open in Notepad and you may be prompted to Restart.(See Extra Note)
- The log is automatically saved by MBAM and can be viewed by clicking the Logs tab in MBAM.
- Copy&Paste the entire report in your next reply.
Extra Note:
If MBAM encounters a file that is difficult to remove,you will be presented with 1 of 2 prompts,click OK to either and let MBAM proceed with the disinfection process,if asked to restart the computer,please do so immediatly.
Go to Kaspersky website and perform an online antivirus scan.
- Read through the requirements and privacy statement and click on Accept button.
- It will start downloading and installing the scanner and virus definitions. You will be prompted to install an application from Kaspersky. Click Run.
- When the downloads have finished, click on Settings.
- Make sure these boxes are checked (ticked). If they are not, please tick them and click on the Save button:
- Spyware, Adware, Dialers, and other potentially dangerous programs
Archives
Mail databases
- Spyware, Adware, Dialers, and other potentially dangerous programs
[*]Click on My Computer under Scan.
[*]Once the scan is complete, it will display the results. Click on View Scan Report.
[*]You will see a list of infected items there. Click on Save Report As....
[*]Save this report to a convenient place. Change the Files of type to Text file (.txt) before clicking on the Save button. Then post it here.
- Open the file and close any other windows.
-
I can not get back onto the kapersky site, as my power went our during download. The mbam log is as follows....
Malwarebytes' Anti-Malware 1.46
www.malwarebytes.org
Database version: 5103
Windows 5.1.2600 Service Pack 3
Internet Explorer 8.0.6001.18702
11/12/2010 6:17:07 PM
mbam-log-2010-11-12 (18-17-07).txt
Scan type: Quick scan
Objects scanned: 151152
Time elapsed: 26 minute(s), 7 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 0
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
(No malicious items detected)
Download TFC to your desktop
- Open the file and close any other windows.
- It will close all programs itself when run, make sure to let it run uninterrupted.
- Click the Start button to begin the process. The program should not take long to finish its job
- Once its finished it should reboot your machine, if not, do this yourself to ensure a complete clean
Please download Malwarebytes' Anti-Malware from Here
Double Click mbam-setup.exe to install the application.
- Make sure a checkmark is placed next to Update Malwarebytes' Anti-Malware and Launch Malwarebytes' Anti-Malware, then click Finish.
- If an update is found, it will download and install the latest version.
- Once the program has loaded, select "Perform Quick Scan", then click Scan.
- The scan may take some time to finish,so please be patient.
- When the scan is complete, click OK, then Show Results to view the results.
- Make sure that everything is checked, and click Remove Selected.
- When disinfection is completed, a log will open in Notepad and you may be prompted to Restart.(See Extra Note)
- The log is automatically saved by MBAM and can be viewed by clicking the Logs tab in MBAM.
- Copy&Paste the entire report in your next reply.
Extra Note:
If MBAM encounters a file that is difficult to remove,you will be presented with 1 of 2 prompts,click OK to either and let MBAM proceed with the disinfection process,if asked to restart the computer,please do so immediatly.
Go to Kaspersky website and perform an online antivirus scan.
- Read through the requirements and privacy statement and click on Accept button.
- It will start downloading and installing the scanner and virus definitions. You will be prompted to install an application from Kaspersky. Click Run.
- When the downloads have finished, click on Settings.
- Make sure these boxes are checked (ticked). If they are not, please tick them and click on the Save button:
- Spyware, Adware, Dialers, and other potentially dangerous programs
Archives
Mail databases
- Spyware, Adware, Dialers, and other potentially dangerous programs
[*]Click on My Computer under Scan.
[*]Once the scan is complete, it will display the results. Click on View Scan Report.
[*]You will see a list of infected items there. Click on Save Report As....
[*]Save this report to a convenient place. Change the Files of type to Text file (.txt) before clicking on the Save button. Then post it here.
- Open the file and close any other windows.
-
ComboFix 10-11-11.01 - Owner 11/12/2010 6:58.2.1 - x86
Microsoft Windows XP Home Edition 5.1.2600.3.1252.1.1033.18.2046.1502 [GMT -5:00]
Running from: c:\documents and settings\Owner\Desktop\ComboFix.exe
AV: Norton Security Suite *On-access scanning disabled* (Updated) {E10A9785-9598-4754-B552-92431C1C35F8}
FW: Norton Security Suite *enabled* {7C21A4C9-F61F-4AC4-B722-A6E19C16F220}
.
((((((((((((((((((((((((( Files Created from 2010-10-12 to 2010-11-12 )))))))))))))))))))))))))))))))
.
2010-11-11 15:33 . 2003-07-16 20:24 4224 -c--a-w- c:\windows\system32\dllcache\beep.sys
2010-11-11 15:33 . 2003-07-16 20:24 4224 ----a-w- c:\windows\system32\drivers\beep.sys
2010-11-11 04:23 . 2010-11-11 04:23 -------- dc----w- C:\_OTL
2010-11-10 17:09 . 2010-11-10 17:09 -------- d-----w- c:\program files\Sophos
2010-11-10 01:58 . 2010-11-10 01:58 -------- dc----w- C:\Rooter$
2010-11-10 01:42 . 2010-04-29 20:39 38224 ----a-w- c:\windows\system32\drivers\mbamswissarmy.sys
2010-11-10 01:41 . 2010-04-29 20:39 20952 ----a-w- c:\windows\system32\drivers\mbam.sys
2010-11-10 01:41 . 2010-11-10 01:42 -------- d-----w- c:\program files\Malwarebytes' Anti-Malware
2010-11-10 01:28 . 2010-11-10 01:28 -------- dc----w- C:\_OTM
2010-11-10 01:12 . 2010-11-10 01:12 388096 ----a-r- c:\documents and settings\Owner\Application Data\Microsoft\Installer\{45A66726-69BC-466B-A7A4-12FCBA4883D7}\HiJackThis.exe
2010-11-10 01:12 . 2010-11-10 01:12 -------- d-----w- c:\program files\Trend Micro
2010-11-06 22:25 . 2010-11-06 22:25 -------- d-----w- c:\documents and settings\Owner\Application Data\PlayPond
2010-11-03 14:37 . 2009-06-30 14:37 28552 ----a-w- c:\windows\system32\drivers\pavboot.sys
2010-11-03 14:35 . 2010-11-03 14:35 -------- d-----w- c:\program files\Panda Security
2010-10-29 02:13 . 2010-10-29 02:14 -------- d-----w- c:\program files\Mystery Legends - The Phantom of the Opera Collector's Edition
2010-10-20 14:56 . 2010-10-20 14:56 -------- d-----w- c:\program files\Microsoft Silverlight
2010-10-18 22:46 . 2010-10-18 22:46 -------- d-----w- C:\Color
2010-10-18 22:46 . 2010-10-18 22:46 -------- d-----w- C:\Custom
2010-10-18 22:45 . 2010-10-18 22:45 -------- d-----w- C:\Fontnav
2010-10-18 22:45 . 2010-10-18 22:45 -------- d-----w- C:\Macros
2010-10-18 22:45 . 2010-10-18 22:45 -------- d-----w- C:\Queries
2010-10-18 22:45 . 2010-10-18 22:46 -------- d-----w- C:\Config
2010-10-18 22:45 . 2010-10-18 22:45 -------- d-----w- C:\XML
2010-10-18 22:44 . 2010-10-18 22:45 -------- d-----w- C:\Template
2010-10-18 22:44 . 2010-10-18 22:46 -------- d-----w- C:\Filters
2010-10-18 22:44 . 2010-10-18 22:45 -------- d-----w- C:\Chart Support Files
2010-10-18 22:44 . 2010-10-18 22:45 -------- d-----w- C:\Graphics
2010-10-18 22:44 . 2010-11-03 15:24 -------- d-----w- C:\Programs
2010-10-18 22:44 . 2010-10-18 22:45 -------- d-----w- C:\Shared
2010-10-18 20:20 . 2010-11-10 12:49 -------- d-----w- c:\documents and settings\All Users\Application Data\WinZip
2010-10-15 21:10 . 2010-10-15 21:10 -------- d-----w- c:\program files\iPod
2010-10-15 21:09 . 2010-10-15 21:11 -------- d-----w- c:\program files\iTunes
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin7.dll
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin6.dll
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin5.dll
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin4.dll
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin3.dll
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin2.dll
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin.dll
2010-10-15 21:02 . 2010-10-15 21:03 -------- d-----w- c:\program files\QuickTime
2010-10-15 20:58 . 2010-10-15 20:58 -------- d-----w- c:\program files\Bonjour
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2010-10-18 22:48 . 2010-09-16 00:29 2516 --sha-w- c:\documents and settings\All Users\Application Data\KGyGaAvL.sys
2010-10-18 22:48 . 2010-09-16 00:29 88 --sh--r- c:\documents and settings\All Users\Application Data\CFD22FE827.sys
2010-09-18 16:23 . 2003-07-16 20:33 974848 ----a-w- c:\windows\system32\mfc42u.dll
2010-09-18 06:53 . 2003-07-16 20:33 974848 ----a-w- c:\windows\system32\mfc42.dll
2010-09-18 06:53 . 2003-07-16 20:33 954368 ----a-w- c:\windows\system32\mfc40.dll
2010-09-18 06:53 . 2003-07-16 20:33 953856 ----a-w- c:\windows\system32\mfc40u.dll
2010-09-15 08:50 . 2010-09-22 15:12 472808 ----a-w- c:\windows\system32\deployJava1.dll
2010-09-15 06:29 . 2010-02-18 23:20 73728 ----a-w- c:\windows\system32\javacpl.cpl
2010-09-10 05:58 . 2006-06-23 16:33 916480 ----a-w- c:\windows\system32\wininet.dll
2010-09-10 05:58 . 2003-07-16 20:32 43520 ----a-w- c:\windows\system32\licmgr10.dll
2010-09-10 05:58 . 2003-07-16 20:30 1469440 ----a-w- c:\windows\system32\inetcpl.cpl
2010-09-08 15:17 . 2010-09-08 15:17 94208 ----a-w- c:\windows\system32\QuickTimeVR.qtx
2010-09-08 15:17 . 2010-09-08 15:17 69632 ----a-w- c:\windows\system32\QuickTime.qts
2010-09-01 11:51 . 2003-07-16 20:24 285824 ----a-w- c:\windows\system32\atmfd.dll
2010-08-31 13:42 . 2003-07-16 20:51 1852800 ----a-w- c:\windows\system32\win32k.sys
2010-08-27 08:02 . 2003-07-16 20:47 119808 ----a-w- c:\windows\system32\t2embed.dll
2010-08-27 05:57 . 2003-07-16 20:46 99840 ----a-w- c:\windows\system32\srvsvc.dll
2010-08-26 13:39 . 2003-07-16 20:46 357248 ----a-w- c:\windows\system32\drivers\srv.sys
2010-08-26 12:52 . 2009-04-16 22:30 5120 ----a-w- c:\windows\system32\xpsp4res.dll
2010-08-23 16:12 . 2003-07-16 20:25 617472 ----a-w- c:\windows\system32\comctl32.dll
2010-08-17 13:17 . 2005-06-10 23:55 58880 ----a-w- c:\windows\system32\spoolsv.exe
2010-08-16 08:45 . 2004-03-06 02:16 590848 ----a-w- c:\windows\system32\rpcrt4.dll
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"BCMSMMSG"="BCMSMMSG.exe" [2003-08-29 122880]
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\winlogon\notify\GoToAssist]
2008-03-14 01:51 10536 ----a-w- c:\program files\Citrix\GoToAssist\508\g2awinlogon.dll
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\SymEFA.sys]
@="FSFilter Activity Monitor"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\Wdf01000.sys]
@="Driver"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\WudfSvc]
@="Service"
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile]
"EnableFirewall"= 0 (0x0)
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"c:\\Program Files\\Sony\\Station\\LaunchPad\\LaunchPad.exe"=
"c:\\Program Files\\Kodak\\Kodak EasyShare software\\bin\\EasyShare.exe"=
"c:\\Program Files\\AIM6\\aim6.exe"=
"c:\\Program Files\\Common Files\\AOL\\Loader\\aolload.exe"=
"c:\\Program Files\\Bonjour\\mDNSResponder.exe"=
"c:\\Program Files\\iTunes\\iTunes.exe"=
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"1525:TCP"= 1525:TCP:Akamai NetSession Interface
"5000:UDP"= 5000:UDP:Akamai NetSession Interface
R0 pavboot;pavboot;c:\windows\system32\drivers\pavboot.sys [11/3/2010 9:37 AM 28552]
R0 SymEFA;Symantec Extended File Attributes;c:\windows\system32\drivers\N360\0308000.029\SymEFA.sys [2/25/2010 2:09 PM 310320]
R1 BHDrvx86;Symantec Heuristics Driver;c:\windows\system32\drivers\N360\0308000.029\BHDrvx86.sys [2/25/2010 2:09 PM 259632]
R1 ccHP;Symantec Hash Provider;c:\windows\system32\drivers\N360\0308000.029\cchpx86.sys [2/25/2010 2:09 PM 482432]
R1 IDSxpx86;IDSxpx86;c:\documents and settings\All Users\Application Data\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\Norton\Definitions\IPSDefs\20101111.001\IDSXpx86.sys [10/19/2010 3:36 PM 341880]
R2 N360;Norton Security Suite;c:\program files\Norton Security Suite\Engine\3.8.0.41\ccSvcHst.exe [2/25/2010 2:09 PM 117640]
R2 Viewpoint Manager Service;Viewpoint Manager Service;c:\program files\Viewpoint\Common\ViewpointService.exe [6/16/2009 8:16 PM 24652]
R3 EraserUtilRebootDrv;EraserUtilRebootDrv;c:\program files\Common Files\Symantec Shared\EENGINE\EraserUtilRebootDrv.sys [11/8/2010 10:35 AM 102448]
S3 EraserUtilDrvI9;EraserUtilDrvI9;\??\c:\program files\Common Files\Symantec Shared\EENGINE\EraserUtilDrvI9.sys --> c:\program files\Common Files\Symantec Shared\EENGINE\EraserUtilDrvI9.sys [?]
S3 MEMSWEEP2;MEMSWEEP2;\??\c:\windows\system32\19.tmp --> c:\windows\system32\19.tmp [?]
--- Other Services/Drivers In Memory ---
*NewlyCreated* - KLMD25
*Deregistered* - klmd25
*Deregistered* - uphcleanhlp
.
Contents of the 'Scheduled Tasks' folder
2010-11-05 c:\windows\Tasks\AppleSoftwareUpdate.job
- c:\program files\Apple Software Update\SoftwareUpdate.exe [2009-10-22 15:50]
.
.
------- Supplementary Scan -------
.
uStart Page = hxxp://www.comcast.net/
uSearchMigratedDefaultURL = hxxp://www.google.com/search?q={searchTerms}&sourceid=ie7&rls=com.microsoft:en-US&ie=utf8&oe=utf8
uInternet Connection Wizard,ShellNext = iexplore
uInternet Settings,ProxyOverride = *.local
IE: E&xport to Microsoft Excel - c:\progra~1\MICROS~4\Office12\EXCEL.EXE/3000
IE: Google Sidewiki... - c:\program files\Google\Google Toolbar\Component\GoogleToolbarDynamic_mui_en_89D8574934B26AC4.dll/cmsidewiki.html
IE: Open with WordPerfect - c:\program files\Corel\WordPerfect Office X5\Programs\WPLauncher.hta
Trusted Zone: internet
Trusted Zone: mcafee.com
DPF: {924B4927-D3BA-41EA-9F7E-8A89194AB3AC} - hxxp://panda-plugin.disney.go.com/plugin/win32/p3dactivex.cab
.
**************************************************************************
catchme 0.3.1398 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2010-11-12 07:04
Windows 5.1.2600 Service Pack 3 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
[HKEY_LOCAL_MACHINE\System\ControlSet002\Services\N360]
"ImagePath"="\"c:\program files\Norton Security Suite\Engine\3.8.0.41\ccSvcHst.exe\" /s \"N360\" /m \"c:\program files\Norton Security Suite\Engine\3.8.0.41\diMaster.dll\" /prefetch:1"
[HKEY_LOCAL_MACHINE\System\ControlSet002\Services\MEMSWEEP2]
"ImagePath"="\??\c:\windows\system32\19.tmp"
.
--------------------- LOCKED REGISTRY KEYS ---------------------
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}]
@Denied: (A 2) (Everyone)
@="FlashBroker"
"LocalizedString"="@c:\\WINDOWS\\system32\\Macromed\\Flash\\FlashUtil10k_ActiveX.exe,-101"
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\Elevation]
"Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\LocalServer32]
@="c:\\WINDOWS\\system32\\Macromed\\Flash\\FlashUtil10k_ActiveX.exe"
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}]
@Denied: (A 2) (Everyone)
@="IFlashBroker4"
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\ProxyStubClsid32]
@="{00020424-0000-0000-C000-000000000046}"
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
"Version"="1.0"
.
--------------------- DLLs Loaded Under Running Processes ---------------------
- - - - - - - > 'winlogon.exe'(888)
c:\program files\Citrix\GoToAssist\508\G2AWinLogon.dll
- - - - - - - > 'explorer.exe'(1844)
c:\windows\system32\WININET.dll
c:\windows\WinSxS\x86_Microsoft.VC80.CRT_1fc8b3b9a1e18e3b_8.0.50727.4053_x-ww_e6967989\MSVCR80.dll
c:\windows\system32\ieframe.dll
c:\windows\system32\webcheck.dll
c:\windows\system32\WPDShServiceObj.dll
c:\windows\system32\PortableDeviceTypes.dll
c:\windows\system32\PortableDeviceApi.dll
.
Completion time: 2010-11-12 07:09:33
ComboFix-quarantined-files.txt 2010-11-12 12:09
ComboFix2.txt 2010-11-11 15:38
Pre-Run: 16,485,257,216 bytes free
Post-Run: 16,516,083,712 bytes free
- - End Of File - - 208A0122529AFEAB66AD3FEE8D3649E0
run combofix again and post its log
-
OTL logfile created on: 11/11/2010 6:04:37 PM - Run 2
OTL by OldTimer - Version 3.2.17.3 Folder = C:\Documents and Settings\Owner\Desktop
Windows XP Home Edition Service Pack 3 (Version = 5.1.2600) - Type = NTWorkstation
Internet Explorer (Version = 8.0.6001.18702)
Locale: 00000409 | Country: United States | Language: ENU | Date Format: M/d/yyyy
2.00 Gb Total Physical Memory | 1.00 Gb Available Physical Memory | 62.00% Memory free
2.00 Gb Paging File | 2.00 Gb Available in Paging File | 79.00% Paging File free
Paging file location(s): C:\pagefile.sys 576 1152 [binary data]
%SystemDrive% = C: | %SystemRoot% = C:\WINDOWS | %ProgramFiles% = C:\Program Files
Drive C: | 37.26 Gb Total Space | 15.40 Gb Free Space | 41.33% Space Free | Partition Type: NTFS
Drive D: | 533.31 Mb Total Space | 0.00 Mb Free Space | 0.00% Space Free | Partition Type: CDFS
Drive F: | 931.51 Gb Total Space | 899.77 Gb Free Space | 96.59% Space Free | Partition Type: NTFS
Computer Name: BIGDADDYCVK | User Name: Owner | Logged in as Administrator.
Boot Mode: Normal | Scan Mode: Current user
Company Name Whitelist: Off | Skip Microsoft Files: Off | No Company Name Whitelist: Off | File Age = 30 Days
========== Standard Registry (All) ==========
========== Internet Explorer ==========
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Default_Page_URL = http://go.microsoft.com/fwlink/?LinkId=69157
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Default_Search_URL = http://go.microsoft.com/fwlink/?LinkId=54896
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Default_Secondary_Page_URL = [binary data]
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Extensions Off Page = about:NoAdd-ons
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Local Page = C:\WINDOWS\system32\blank.htm
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Search Page = http://go.microsoft.com/fwlink/?LinkId=54896
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Security Risk Page = about:SecurityRisk
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Start Page = http://go.microsoft.com/fwlink/?LinkId=69157
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Search,CustomizeSearch = http://ie.search.msn.com/{SUB_RFC1766}/srchasst/srchcust.htm
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Search,SearchAssistant = http://ie.search.msn.com/{SUB_RFC1766}/srchasst/srchasst.htm
IE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,Local Page = C:\WINDOWS\system32\blank.htm
IE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,Page_Transitions = 1
IE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,Search Page = http://www.microsoft.com/isapi/redir.dll?prd=ie&ar=iesearch
IE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,SearchMigratedDefaultName = Google
IE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,SearchMigratedDefaultURL = http://www.google.com/search?q={searchTerms}&sourceid=ie7&rls=com.microsoft:en-US&ie=utf8&oe=utf8
IE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,Start Page = http://www.comcast.net/
IE - HKCU\..\URLSearchHook: - Reg Error: Key error. File not found
IE - HKCU\..\URLSearchHook: {CFBFAE00-17A6-11D0-99CB-00C04FD64497} - C:\WINDOWS\system32\ieframe.dll (Microsoft Corporation)
IE - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyEnable" = 0
IE - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyOverride" = *.local
========== FireFox ==========
FF - prefs.js..browser.search.selectedEngine: "Yahoo!"
FF - prefs.js..extensions.enabledItems: {8545daff-ad1e-493f-a37e-eed1ac79682b}:1.0
FF - prefs.js..extensions.enabledItems: {CAFEEFAC-0016-0000-0018-ABCDEFFEDCBA}:6.0.18
FF - prefs.js..extensions.enabledItems: {20a82645-c095-46ed-80e3-08825760534b}:1.1
FF - prefs.js..extensions.enabledItems: [email protected]:1.0
FF - prefs.js..extensions.enabledItems: {7BA52691-1876-45ce-9EE6-54BCB3B04BBC}:3.7.2
FF - prefs.js..extensions.enabledItems: [email protected]:3.6.6.117
FF - prefs.js..extensions.enabledItems: {972ce4c6-7e08-4474-a285-3208198ce6fd}:3.6
FF - HKLM\software\mozilla\Firefox\extensions\\{3112ca9c-de6d-4884-a869-9855de68056c}: C:\Documents and Settings\All Users\Application Data\Mozilla\Firefox Extensions\{3112ca9c-de6d-4884-a869-9855de68056c} [2009/03/21 13:26:44 | 000,000,000 | ---D | M]
FF - HKLM\software\mozilla\Firefox\extensions\\{20a82645-c095-46ed-80e3-08825760534b}: c:\WINDOWS\Microsoft.NET\Framework\v3.5\Windows Presentation Foundation\DotNetAssistantExtension\ [2009/08/08 13:17:27 | 000,000,000 | ---D | M]
FF - HKLM\software\mozilla\Firefox\extensions\\[email protected]: C:\Program Files\MSN Toolbar\Platform\4.0.0379.0\Firefox
FF - HKLM\software\mozilla\Firefox\extensions\\{7BA52691-1876-45ce-9EE6-54BCB3B04BBC}: C:\Documents and Settings\All Users\Application Data\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\Norton\coFFPlgn\ [2010/04/25 13:47:47 | 000,000,000 | ---D | M]
FF - HKLM\software\mozilla\Firefox\extensions\\[email protected]: C:\Program Files\Java\jre6\lib\deploy\jqs\ff [2010/02/18 18:19:58 | 000,000,000 | ---D | M]
[2010/02/18 18:25:18 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Owner\Application Data\Mozilla\Extensions
[2010/09/30 11:31:15 | 000,000,000 | ---D | M] (No name found) -- C:\Documents and Settings\Owner\Application Data\Mozilla\Extensions\{ec8030f7-c20a-464f-9b0e-13a3a9e97384}
[2009/03/28 11:28:35 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Owner\Application Data\Mozilla\Extensions\[email protected]
[2010/03/10 10:22:01 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Owner\Application Data\Mozilla\Firefox\Profiles\r9n0jygc.default\extensions
[2010/02/18 19:54:08 | 000,000,000 | ---D | M] (Microsoft .NET Framework Assistant) -- C:\Documents and Settings\Owner\Application Data\Mozilla\Firefox\Profiles\r9n0jygc.default\extensions\{20a82645-c095-46ed-80e3-08825760534b}
[2010/03/10 10:22:49 | 000,000,000 | ---D | M] -- C:\Program Files\Mozilla Firefox\extensions
[2008/07/30 15:34:27 | 000,000,000 | ---D | M] (Google Toolbar for Firefox) -- C:\Program Files\Mozilla Firefox\extensions\{3112ca9c-de6d-4884-a869-9855de68056c}
[2010/02/18 18:20:27 | 000,000,000 | ---D | M] (Java Console) -- C:\Program Files\Mozilla Firefox\extensions\{CAFEEFAC-0016-0000-0018-ABCDEFFEDCBA}
[2010/02/18 18:19:56 | 000,411,368 | ---- | M] (Sun Microsystems, Inc.) -- C:\Program Files\Mozilla Firefox\plugins\npdeploytk.dll
[2006/10/26 20:12:16 | 000,016,192 | ---- | M] (Microsoft Corporation) -- C:\Program Files\Mozilla Firefox\plugins\NPOFF12.DLL
[2010/02/25 00:51:16 | 000,002,221 | ---- | M] () -- C:\Program Files\Mozilla Firefox\searchplugins\SafeSearch.xml
[2009/04/07 12:59:38 | 000,000,872 | ---- | M] () -- C:\Program Files\Mozilla Firefox\searchplugins\Yahooober253188250.gif
[2010/05/14 17:31:04 | 000,000,196 | ---- | M] () -- C:\Program Files\Mozilla Firefox\searchplugins\Yahooober253188250.src
O1 HOSTS File: ([2010/11/11 10:33:52 | 000,000,027 | ---- | M]) - C:\WINDOWS\system32\drivers\etc\hosts
O1 - Hosts: 127.0.0.1 localhost
O2 - BHO: (Adobe PDF Link Helper) - {18DF081C-E8AD-4283-A596-FA578C2EBDC3} - C:\Program Files\Common Files\Adobe\Acrobat\ActiveX\AcroIEHelperShim.dll (Adobe Systems Incorporated)
O2 - BHO: (Spybot-S&D IE Protection) - {53707962-6F74-2D53-2644-206D7942484F} - C:\Program Files\Spybot - Search & Destroy\SDHelper.dll (Safer Networking Limited)
O2 - BHO: (Symantec NCO BHO) - {602ADB0E-4AFF-4217-8AA1-95DAC4DFA408} - C:\Program Files\Norton Security Suite\Engine\3.8.0.41\CoIEPlg.dll (Symantec Corporation)
O2 - BHO: (Symantec Intrusion Prevention) - {6D53EC84-6AAE-4787-AEEE-F4628F01010C} - C:\Program Files\Norton Security Suite\Engine\3.8.0.41\IPSBHO.dll (Symantec Corporation)
O2 - BHO: (Windows Live ID Sign-in Helper) - {9030D464-4C02-4ABF-8ECC-5164760863C6} - C:\Program Files\Common Files\Microsoft Shared\Windows Live\WindowsLiveLogin.dll (Microsoft Corporation)
O2 - BHO: (no name) - {d2ce3e00-f94a-4740-988e-03dc2f38c34f} - No CLSID value found.
O2 - BHO: (Java Plug-In 2 SSV Helper) - {DBC80044-A445-435b-BC74-9C25C1C588A9} - C:\Program Files\Java\jre6\bin\jp2ssv.dll (Sun Microsystems, Inc.)
O2 - BHO: (JQSIEStartDetectorImpl Class) - {E7E6F031-17CE-4C07-BC86-EABFE594F69C} - C:\Program Files\Java\jre6\lib\deploy\jqs\ie\jqs_plugin.dll (Sun Microsystems, Inc.)
O3 - HKLM\..\Toolbar: (Norton Toolbar) - {7FEBEFE3-6B19-4349-98D2-FFB09D4B49CA} - C:\Program Files\Norton Security Suite\Engine\3.8.0.41\CoIEPlg.dll (Symantec Corporation)
O3 - HKCU\..\Toolbar\WebBrowser: (&Address) - {01E04581-4EEE-11D0-BFE9-00AA005B4383} - C:\WINDOWS\system32\browseui.dll (Microsoft Corporation)
O3 - HKCU\..\Toolbar\WebBrowser: (&Links) - {0E5CBF21-D15F-11D0-8301-00AA005B4383} - C:\WINDOWS\system32\shell32.dll (Microsoft Corporation)
O3 - HKCU\..\Toolbar\WebBrowser: (Norton Toolbar) - {7FEBEFE3-6B19-4349-98D2-FFB09D4B49CA} - C:\Program Files\Norton Security Suite\Engine\3.8.0.41\CoIEPlg.dll (Symantec Corporation)
O4 - HKLM..\Run: [bCMSMMSG] C:\WINDOWS\BCMSMMSG.exe (Broadcom Corporation)
O4 - Startup: C:\Documents and Settings\All Users\Start Menu\Programs\Startup\Kodak EasyShare software.lnk = C:\Program Files\Kodak\Kodak EasyShare software\bin\EasyShare.exe (Eastman Kodak Company)
O4 - Startup: C:\Documents and Settings\Owner\Start Menu\Programs\Startup\ERUNT AutoBackup.lnk = C:\Program Files\ERUNT\AUTOBACK.EXE ()
O6 - HKLM\Software\Policies\Microsoft\Internet Explorer\Restrictions present
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: HonorAutoRunSetting = 1
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoDriveAutoRun = 67108863
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoDriveTypeAutoRun = 323
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoDrives = 0
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: dontdisplaylastusername = 0
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: legalnoticecaption =
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: legalnoticetext =
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: shutdownwithoutlogon = 1
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: undockwithoutlogon = 1
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: DisableRegistryTools = 0
O7 - HKCU\Software\Policies\Microsoft\Internet Explorer\Control Panel present
O7 - HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoDriveTypeAutoRun = 323
O7 - HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoDriveAutoRun = 67108863
O7 - HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoDrives = 0
O9 - Extra 'Tools' menuitem : Spybot - Search & Destroy Configuration - {DFB852A3-47F8-48C4-A200-58CAB36FD2A2} - C:\Program Files\Spybot - Search & Destroy\SDHelper.dll (Safer Networking Limited)
O9 - Extra 'Tools' menuitem : @xpsp3res.dll,-20001 - {e2e2dd38-d088-4134-82b7-f2ba38496583} - C:\WINDOWS\network diagnostic\xpnetdiag.exe (Microsoft Corporation)
O9 - Extra Button: Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe (Microsoft Corporation)
O9 - Extra 'Tools' menuitem : Windows Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe (Microsoft Corporation)
O10 - NameSpace_Catalog5\Catalog_Entries\000000000001 [] - C:\WINDOWS\system32\mswsock.dll (Microsoft Corporation)
O10 - NameSpace_Catalog5\Catalog_Entries\000000000002 [] - C:\WINDOWS\system32\winrnr.dll (Microsoft Corporation)
O10 - NameSpace_Catalog5\Catalog_Entries\000000000003 [] - C:\WINDOWS\system32\mswsock.dll (Microsoft Corporation)
O10 - NameSpace_Catalog5\Catalog_Entries\000000000004 [] - C:\Program Files\Bonjour\mdnsNSP.dll (Apple Inc.)
O10 - Protocol_Catalog9\Catalog_Entries\000000000001 - C:\WINDOWS\system32\mswsock.dll (Microsoft Corporation)
O10 - Protocol_Catalog9\Catalog_Entries\000000000002 - C:\WINDOWS\system32\mswsock.dll (Microsoft Corporation)
O10 - Protocol_Catalog9\Catalog_Entries\000000000003 - C:\WINDOWS\system32\mswsock.dll (Microsoft Corporation)
O10 - Protocol_Catalog9\Catalog_Entries\000000000004 - C:\WINDOWS\system32\rsvpsp.dll (Microsoft Corporation)
O10 - Protocol_Catalog9\Catalog_Entries\000000000005 - C:\WINDOWS\system32\rsvpsp.dll (Microsoft Corporation)
O10 - Protocol_Catalog9\Catalog_Entries\000000000006 - C:\WINDOWS\system32\mswsock.dll (Microsoft Corporation)
O10 - Protocol_Catalog9\Catalog_Entries\000000000007 - C:\WINDOWS\system32\mswsock.dll (Microsoft Corporation)
O10 - Protocol_Catalog9\Catalog_Entries\000000000008 - C:\WINDOWS\system32\mswsock.dll (Microsoft Corporation)
O10 - Protocol_Catalog9\Catalog_Entries\000000000009 - C:\WINDOWS\system32\mswsock.dll (Microsoft Corporation)
O10 - Protocol_Catalog9\Catalog_Entries\000000000010 - C:\WINDOWS\system32\mswsock.dll (Microsoft Corporation)
O10 - Protocol_Catalog9\Catalog_Entries\000000000011 - C:\WINDOWS\system32\mswsock.dll (Microsoft Corporation)
O15 - HKCU\..Trusted Domains: internet ([]about in Trusted sites)
O15 - HKCU\..Trusted Domains: mcafee.com ([]http in Trusted sites)
O15 - HKCU\..Trusted Domains: mcafee.com ([]https in Trusted sites)
O16 - DPF: {02BF25D5-8C17-4B23-BC80-D3488ABDDC6B} http://appldnld.apple.com.edgesuite.net/content.info.apple.com/QuickTime/qtactivex/qtplugin.cab (QuickTime Object)
O16 - DPF: {0CCA191D-13A6-4E29-B746-314DEE697D83} http://upload.facebook.com/controls/2008.10.10_v5.5.8/FacebookPhotoUploader5.cab (Facebook Photo Uploader 5 Control)
O16 - DPF: {48DD0448-9209-4F81-9F6D-D83562940134} http://lads.myspace.com/upload/MySpaceUploader1006.cab (MySpace Uploader Control)
O16 - DPF: {6E32070A-766D-4EE6-879C-DC1FA91D2FC3} http://www.update.microsoft.com/microsoftupdate/v6/V5Controls/en/x86/client/muweb_site.cab?1205858423406 (MUWebControl Class)
O16 - DPF: {8AD9C840-044E-11D1-B3E9-00805F499D93} http://java.sun.com/update/1.6.0/jinstall-1_6_0_22-windows-i586.cab (Java Plug-in 1.6.0_22)
O16 - DPF: {8FFBE65D-2C9C-4669-84BD-5829DC0B603C} http://fpdownload.macromedia.com/get/flashplayer/current/polarbear/ultrashim.cab (Reg Error: Key error.)
O16 - DPF: {9191F686-7F0A-441D-8A98-2FE3AC1BD913} http://acs.pandasoftware.com/activescan/cabs/as2stubie.cab (ActiveScan 2.0 Installer Class)
O16 - DPF: {924B4927-D3BA-41EA-9F7E-8A89194AB3AC} http://panda-plugin.disney.go.com/plugin/win32/p3dactivex.cab (P3DActiveX Control)
O16 - DPF: {CAFEEFAC-0016-0000-0022-ABCDEFFEDCBA} http://java.sun.com/update/1.6.0/jinstall-1_6_0_22-windows-i586.cab (Java Plug-in 1.6.0_22)
O16 - DPF: {CAFEEFAC-FFFF-FFFF-FFFF-ABCDEFFEDCBA} http://java.sun.com/update/1.6.0/jinstall-1_6_0_22-windows-i586.cab (Java Plug-in 1.6.0_22)
O16 - DPF: {E2883E8F-472F-4FB0-9522-AC9BF37916A7} http://platformdl.adobe.com/NOS/getPlusPlus/1.6/gp.cab (Reg Error: Key error.)
O17 - HKLM\System\CCS\Services\Tcpip\Parameters: DhcpNameServer = 192.168.1.1
O18 - Protocol\Handler\about {3050F406-98B5-11CF-BB82-00AA00BDCE0B} - C:\WINDOWS\system32\mshtml.dll (Microsoft Corporation)
O18 - Protocol\Handler\cdl {3dd53d40-7b8b-11D0-b013-00aa0059ce02} - C:\WINDOWS\system32\urlmon.dll (Microsoft Corporation)
O18 - Protocol\Handler\dvd {12D51199-0DB5-46FE-A120-47A3D7D937CC} - C:\WINDOWS\system32\msvidctl.dll (Microsoft Corporation)
O18 - Protocol\Handler\file {79eac9e7-baf9-11ce-8c82-00aa004ba90b} - C:\WINDOWS\system32\urlmon.dll (Microsoft Corporation)
O18 - Protocol\Handler\ftp {79eac9e3-baf9-11ce-8c82-00aa004ba90b} - C:\WINDOWS\system32\urlmon.dll (Microsoft Corporation)
O18 - Protocol\Handler\gopher {79eac9e4-baf9-11ce-8c82-00aa004ba90b} - C:\WINDOWS\system32\urlmon.dll (Microsoft Corporation)
O18 - Protocol\Handler\http {79eac9e2-baf9-11ce-8c82-00aa004ba90b} - C:\WINDOWS\system32\urlmon.dll (Microsoft Corporation)
O18 - Protocol\Handler\http\0x00000001 {E1D2BF42-A96B-11d1-9C6B-0000F875AC61} - C:\Program Files\Common Files\System\Ole DB\MSDAIPP.DLL (Microsoft Corporation)
O18 - Protocol\Handler\http\oledb {E1D2BF40-A96B-11d1-9C6B-0000F875AC61} - C:\Program Files\Common Files\System\Ole DB\MSDAIPP.DLL (Microsoft Corporation)
O18 - Protocol\Handler\https {79eac9e5-baf9-11ce-8c82-00aa004ba90b} - C:\WINDOWS\system32\urlmon.dll (Microsoft Corporation)
O18 - Protocol\Handler\https\0x00000001 {E1D2BF42-A96B-11d1-9C6B-0000F875AC61} - C:\Program Files\Common Files\System\Ole DB\MSDAIPP.DLL (Microsoft Corporation)
O18 - Protocol\Handler\https\oledb {E1D2BF40-A96B-11d1-9C6B-0000F875AC61} - C:\Program Files\Common Files\System\Ole DB\MSDAIPP.DLL (Microsoft Corporation)
O18 - Protocol\Handler\ipp - No CLSID value found
O18 - Protocol\Handler\ipp\0x00000001 {E1D2BF42-A96B-11d1-9C6B-0000F875AC61} - C:\Program Files\Common Files\System\Ole DB\MSDAIPP.DLL (Microsoft Corporation)
O18 - Protocol\Handler\its {9D148291-B9C8-11D0-A4CC-0000F80149F6} - C:\WINDOWS\system32\itss.dll (Microsoft Corporation)
O18 - Protocol\Handler\javascript {3050F3B2-98B5-11CF-BB82-00AA00BDCE0B} - C:\WINDOWS\system32\mshtml.dll (Microsoft Corporation)
O18 - Protocol\Handler\local {79eac9e7-baf9-11ce-8c82-00aa004ba90b} - C:\WINDOWS\system32\urlmon.dll (Microsoft Corporation)
O18 - Protocol\Handler\mailto {3050f3DA-98B5-11CF-BB82-00AA00BDCE0B} - C:\WINDOWS\system32\mshtml.dll (Microsoft Corporation)
O18 - Protocol\Handler\mhtml {05300401-BCBC-11d0-85E3-00C04FD85AB4} - C:\WINDOWS\system32\inetcomm.dll (Microsoft Corporation)
O18 - Protocol\Handler\mk {79eac9e6-baf9-11ce-8c82-00aa004ba90b} - C:\WINDOWS\system32\urlmon.dll (Microsoft Corporation)
O18 - Protocol\Handler\msdaipp - No CLSID value found
O18 - Protocol\Handler\msdaipp\0x00000001 {E1D2BF42-A96B-11d1-9C6B-0000F875AC61} - C:\Program Files\Common Files\System\Ole DB\MSDAIPP.DLL (Microsoft Corporation)
O18 - Protocol\Handler\msdaipp\oledb {E1D2BF40-A96B-11d1-9C6B-0000F875AC61} - C:\Program Files\Common Files\System\Ole DB\MSDAIPP.DLL (Microsoft Corporation)
O18 - Protocol\Handler\ms-its {9D148291-B9C8-11D0-A4CC-0000F80149F6} - C:\WINDOWS\system32\itss.dll (Microsoft Corporation)
O18 - Protocol\Handler\res {3050F3BC-98B5-11CF-BB82-00AA00BDCE0B} - C:\WINDOWS\system32\mshtml.dll (Microsoft Corporation)
O18 - Protocol\Handler\symres {AA1061FE-6C41-421f-9344-69640C9732AB} - C:\Program Files\Norton Security Suite\Engine\3.8.0.41\CoIEPlg.dll (Symantec Corporation)
O18 - Protocol\Handler\sysimage {76E67A63-06E9-11D2-A840-006008059382} - C:\WINDOWS\system32\mshtml.dll (Microsoft Corporation)
O18 - Protocol\Handler\tv {CBD30858-AF45-11D2-B6D6-00C04FBBDE6E} - C:\WINDOWS\system32\msvidctl.dll (Microsoft Corporation)
O18 - Protocol\Handler\vbscript {3050F3B2-98B5-11CF-BB82-00AA00BDCE0B} - C:\WINDOWS\system32\mshtml.dll (Microsoft Corporation)
O18 - Protocol\Handler\wia {13F3EA8B-91D7-4F0A-AD76-D2853AC8BECE} - C:\WINDOWS\system32\wiascr.dll (Microsoft Corporation)
O18 - Protocol\Filter\application/octet-stream {1E66F26B-79EE-11D2-8710-00C04F79ED0D} - C:\WINDOWS\System32\mscoree.dll (Microsoft Corporation)
O18 - Protocol\Filter\application/x-complus {1E66F26B-79EE-11D2-8710-00C04F79ED0D} - C:\WINDOWS\System32\mscoree.dll (Microsoft Corporation)
O18 - Protocol\Filter\application/x-msdownload {1E66F26B-79EE-11D2-8710-00C04F79ED0D} - C:\WINDOWS\System32\mscoree.dll (Microsoft Corporation)
O18 - Protocol\Filter\Class Install Handler {32B533BB-EDAE-11d0-BD5A-00AA00B92AF1} - C:\WINDOWS\system32\urlmon.dll (Microsoft Corporation)
O18 - Protocol\Filter\deflate {8f6b0360-b80d-11d0-a9b3-006097942311} - C:\WINDOWS\system32\urlmon.dll (Microsoft Corporation)
O18 - Protocol\Filter\gzip {8f6b0360-b80d-11d0-a9b3-006097942311} - C:\WINDOWS\system32\urlmon.dll (Microsoft Corporation)
O18 - Protocol\Filter\lzdhtml {8f6b0360-b80d-11d0-a9b3-006097942311} - C:\WINDOWS\system32\urlmon.dll (Microsoft Corporation)
O18 - Protocol\Filter\text/webviewhtml {733AC4CB-F1A4-11d0-B951-00A0C90312E1} - C:\WINDOWS\system32\shell32.dll (Microsoft Corporation)
O20 - HKLM Winlogon: Shell - (Explorer.exe) - C:\WINDOWS\explorer.exe (Microsoft Corporation)
O20 - HKLM Winlogon: UserInit - (C:\WINDOWS\system32\userinit.exe) - C:\WINDOWS\system32\userinit.exe (Microsoft Corporation)
O20 - HKLM Winlogon: UIHost - (logonui.exe) - C:\WINDOWS\System32\logonui.exe (Microsoft Corporation)
O20 - HKLM Winlogon: VMApplet - (rundll32 shell32) - C:\WINDOWS\System32\shell32.dll (Microsoft Corporation)
O20 - HKLM Winlogon: VMApplet - (Control_RunDLL "sysdm.cpl") - C:\WINDOWS\System32\sysdm.cpl (Microsoft Corporation)
O20 - Winlogon\Notify\crypt32chain: DllName - crypt32.dll - C:\WINDOWS\System32\crypt32.dll (Microsoft Corporation)
O20 - Winlogon\Notify\cryptnet: DllName - cryptnet.dll - C:\WINDOWS\System32\cryptnet.dll (Microsoft Corporation)
O20 - Winlogon\Notify\cscdll: DllName - cscdll.dll - C:\WINDOWS\System32\cscdll.dll (Microsoft Corporation)
O20 - Winlogon\Notify\dimsntfy: DllName - %SystemRoot%\System32\dimsntfy.dll - C:\WINDOWS\system32\dimsntfy.dll (Microsoft Corporation)
O20 - Winlogon\Notify\GoToAssist: DllName - C:\Program Files\Citrix\GoToAssist\508\G2AWinLogon.dll - C:\Program Files\Citrix\GoToAssist\508\g2awinlogon.dll (Citrix Online, a division of Citrix Systems, Inc.)
O20 - Winlogon\Notify\igfxcui: DllName - igfxsrvc.dll - C:\WINDOWS\System32\igfxsrvc.dll (Intel Corporation)
O20 - Winlogon\Notify\ScCertProp: DllName - wlnotify.dll - C:\WINDOWS\System32\wlnotify.dll (Microsoft Corporation)
O20 - Winlogon\Notify\Schedule: DllName - wlnotify.dll - C:\WINDOWS\System32\wlnotify.dll (Microsoft Corporation)
O20 - Winlogon\Notify\sclgntfy: DllName - sclgntfy.dll - C:\WINDOWS\System32\sclgntfy.dll (Microsoft Corporation)
O20 - Winlogon\Notify\SensLogn: DllName - WlNotify.dll - C:\WINDOWS\System32\wlnotify.dll (Microsoft Corporation)
O20 - Winlogon\Notify\termsrv: DllName - wlnotify.dll - C:\WINDOWS\System32\wlnotify.dll (Microsoft Corporation)
O20 - Winlogon\Notify\wlballoon: DllName - wlnotify.dll - C:\WINDOWS\System32\wlnotify.dll (Microsoft Corporation)
O21 - SSODL: CDBurn - {fbeb8a05-beee-4442-804e-409d6c4515e9} - C:\WINDOWS\system32\shell32.dll (Microsoft Corporation)
O21 - SSODL: PostBootReminder - {7849596a-48ea-486e-8937-a2a3009f31a9} - C:\WINDOWS\system32\shell32.dll (Microsoft Corporation)
O21 - SSODL: SysTray - {35CEC8A3-2BE6-11D2-8773-92E220524153} - C:\WINDOWS\system32\stobject.dll (Microsoft Corporation)
O21 - SSODL: WebCheck - {E6FB5E20-DE35-11CF-9C87-00AA005127ED} - C:\WINDOWS\system32\webcheck.dll (Microsoft Corporation)
O21 - SSODL: WPDShServiceObj - {AAA288BA-9A4C-45B0-95D7-94D524869DB5} - C:\WINDOWS\system32\WPDShServiceObj.dll (Microsoft Corporation)
O22 - SharedTaskScheduler: {438755C2-A8BA-11D1-B96B-00A0C90312E1} - Browseui preloader - C:\WINDOWS\system32\browseui.dll (Microsoft Corporation)
O22 - SharedTaskScheduler: {8C7461EF-2B13-11d2-BE35-3078302C2030} - Component Categories cache daemon - C:\WINDOWS\system32\browseui.dll (Microsoft Corporation)
O24 - Desktop Components:0 (My Current Home Page) - About:Home
O24 - Desktop WallPaper: C:\Documents and Settings\Owner\Local Settings\Application Data\Microsoft\Wallpaper1.bmp
O24 - Desktop BackupWallPaper: C:\Documents and Settings\Owner\Local Settings\Application Data\Microsoft\Wallpaper1.bmp
O28 - HKLM ShellExecuteHooks: {AEB6717E-7E19-11d0-97EE-00C04FD91972} - C:\WINDOWS\System32\shell32.dll (Microsoft Corporation)
O29 - HKLM SecurityProviders - (msapsspc.dll) - C:\WINDOWS\System32\msapsspc.dll (Microsoft Corporation)
O29 - HKLM SecurityProviders - (schannel.dll) - C:\WINDOWS\System32\schannel.dll (Microsoft Corporation)
O29 - HKLM SecurityProviders - (digest.dll) - C:\WINDOWS\System32\digest.dll (Microsoft Corporation)
O29 - HKLM SecurityProviders - (msnsspc.dll) - C:\WINDOWS\System32\msnsspc.dll (Microsoft Corporation)
O30 - LSA: Authentication Packages - (msv1_0) - C:\WINDOWS\System32\msv1_0.dll (Microsoft Corporation)
O30 - LSA: Security Packages - (kerberos) - C:\WINDOWS\System32\kerberos.dll (Microsoft Corporation)
O30 - LSA: Security Packages - (msv1_0) - C:\WINDOWS\System32\msv1_0.dll (Microsoft Corporation)
O30 - LSA: Security Packages - (schannel) - C:\WINDOWS\System32\schannel.dll (Microsoft Corporation)
O30 - LSA: Security Packages - (wdigest) - C:\WINDOWS\System32\wdigest.dll (Microsoft Corporation)
O31 - SafeBoot: AlternateShell - cmd.exe
O32 - HKLM CDRom: AutoRun - 1
O32 - AutoRun File - [2008/03/13 21:29:54 | 000,000,000 | ---- | M] () - C:\AUTOEXEC.BAT -- [ NTFS ]
O32 - AutoRun File - [2003/07/16 15:55:09 | 000,000,110 | R--- | M] () - D:\AUTORUN.INF -- [ CDFS ]
O32 - AutoRun File - [2010/07/16 20:23:47 | 000,000,000 | R--D | M] - F:\autorun -- [ NTFS ]
O34 - HKLM BootExecute: (autocheck autochk *) - File not found
O35 - HKLM\..comfile [open] -- "%1" %*
O35 - HKLM\..exefile [open] -- "%1" %*
O37 - HKLM\...com [@ = ComFile] -- "%1" %*
O37 - HKLM\...exe [@ = exefile] -- "%1" %*
========== Custom Scans ==========
< MD5 for: BEEP.SYS >
[2003/07/16 15:24:45 | 000,004,224 | ---- | M] (Microsoft Corporation) MD5=DA1F27D85E0D1525F6621372E7B685E9 -- C:\WINDOWS\ERDNT\cache\beep.sys
[2003/07/16 15:24:45 | 000,004,224 | ---- | M] (Microsoft Corporation) MD5=DA1F27D85E0D1525F6621372E7B685E9 -- C:\WINDOWS\system32\dllcache\beep.sys
[2003/07/16 15:24:45 | 000,004,224 | ---- | M] (Microsoft Corporation) MD5=DA1F27D85E0D1525F6621372E7B685E9 -- C:\WINDOWS\system32\drivers\beep.sys
< MD5 for: BEEP.SYS.VIR >
[2008/08/04 15:29:41 | 000,004,080 | ---- | M] (Microsoft Corporation) MD5=DF012C2853281CE2BF536E8DE871C8C1 -- C:\Qoobox\Quarantine\C\WINDOWS\Drivers\beep.sys.vir
[2008/08/04 15:29:41 | 000,004,080 | ---- | M] (Microsoft Corporation) MD5=DF012C2853281CE2BF536E8DE871C8C1 -- C:\Qoobox\Quarantine\C\WINDOWS\system32\drivers\beep.sys.vir
< HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers >
[HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers\Offline Files]
[HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers\OverlayExcluded]
[HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers\OverlayPending]
[HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers\OverlayProtected]
< HKLM\Software\Policies\Microsoft\Windows\System\Scripts /s >
< HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download >
"CheckExeSignatures" = yes
"RunInvalidSignatures" = 0
< HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Telephony\Providers|ProviderFileName6 /rs >
< HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU >
< HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate\Auto Update\Results\Install|LastSuccessTime /rs >
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate\Auto Update\Results\Install\\LastSuccessTime: 2010-11-11 08:01:10
< >
< End of report >
< MD5 for: [2003/07/16 15:24:45 | 000,004,224 | ---- | M] (MICROSOFT CORPORATION) >
[2003/07/16 15:24:45 | 000,004,224 | ---- | M] (Microsoft Corporation) -- C:\WINDOWS\ERDNT\cache\beep.sys
[2003/07/16 15:24:45 | 000,004,224 | ---- | M] (Microsoft Corporation) -- C:\WINDOWS\system32\dllcache\beep.sys
[2003/07/16 15:24:45 | 000,004,224 | ---- | M] (Microsoft Corporation) -- C:\WINDOWS\system32\drivers\beep.sys
< MD5 for: [2008/08/04 15:29:41 | 000,004,080 | ---- | M] (MICROSOFT CORPORATION) >
[2008/08/04 15:29:41 | 000,004,080 | ---- | M] (Microsoft Corporation) -- C:\Qoobox\Quarantine\C\WINDOWS\Drivers\beep.sys.vir
[2008/08/04 15:29:41 | 000,004,080 | ---- | M] (Microsoft Corporation) -- C:\Qoobox\Quarantine\C\WINDOWS\system32\drivers\beep.sys.vir
< HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers >
[HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers\Offline Files]
[HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers\OverlayExcluded]
[HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers\OverlayPending]
[HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers\OverlayProtected]
< HKLM\Software\Policies\Microsoft\Windows\System\Scripts /s >
< HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download >
"CheckExeSignatures" = yes
"RunInvalidSignatures" = 0
< HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Telephony\Providers|ProviderFileName6 /rs >
< HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU >
< HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate\Auto Update\Results\Install|LastSuccessTime /rs >
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate\Auto Update\Results\Install\\LastSuccessTime: 2010-11-11 08:01:10
< >
< End of report >
open OTL click the none button, paste this in the custom scan box
/md5start
beep.*
/md5stop
HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers
HKLM\Software\Policies\Microsoft\Windows\System\Scripts /s
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Telephony\Providers|ProviderFileName6 /rs
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate\Auto Update\Results\Install|LastSuccessTime /rs
click run scan post that log
-
Here it goes! It did instruct me to put in my original Windows XP Home Edition CD, but nothing else happened but the log report populating.
ComboFix 10-11-10.03 - Owner 11/11/2010 10:24:00.1.1 - x86
Microsoft Windows XP Home Edition 5.1.2600.3.1252.1.1033.18.2046.1322 [GMT -5:00]
Running from: c:\documents and settings\Owner\Desktop\ComboFix.exe
AV: Norton Security Suite *On-access scanning disabled* (Updated) {E10A9785-9598-4754-B552-92431C1C35F8}
FW: Norton Security Suite *enabled* {7C21A4C9-F61F-4AC4-B722-A6E19C16F220}
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
c:\program files\Common Files\Uninstall
c:\windows\DRIVERS\beep.sys
c:\windows\heqihaw.exe
c:\windows\wuxulul.exe
F:\Autorun.inf
c:\windows\system32\drivers\beep.sys . . . is infected!!
.
((((((((((((((((((((((((( Files Created from 2010-10-11 to 2010-11-11 )))))))))))))))))))))))))))))))
.
2010-11-11 15:33 . 2003-07-16 20:24 4224 -c--a-w- c:\windows\system32\dllcache\beep.sys
2010-11-11 15:33 . 2003-07-16 20:24 4224 ----a-w- c:\windows\system32\drivers\beep.sys
2010-11-11 04:23 . 2010-11-11 04:23 -------- dc----w- C:\_OTL
2010-11-10 17:09 . 2010-11-10 17:09 -------- d-----w- c:\program files\Sophos
2010-11-10 01:58 . 2010-11-10 01:58 -------- dc----w- C:\Rooter$
2010-11-10 01:42 . 2010-04-29 20:39 38224 ----a-w- c:\windows\system32\drivers\mbamswissarmy.sys
2010-11-10 01:41 . 2010-04-29 20:39 20952 ----a-w- c:\windows\system32\drivers\mbam.sys
2010-11-10 01:41 . 2010-11-10 01:42 -------- d-----w- c:\program files\Malwarebytes' Anti-Malware
2010-11-10 01:28 . 2010-11-10 01:28 -------- dc----w- C:\_OTM
2010-11-10 01:12 . 2010-11-10 01:12 388096 ----a-r- c:\documents and settings\Owner\Application Data\Microsoft\Installer\{45A66726-69BC-466B-A7A4-12FCBA4883D7}\HiJackThis.exe
2010-11-10 01:12 . 2010-11-10 01:12 -------- d-----w- c:\program files\Trend Micro
2010-11-06 22:25 . 2010-11-06 22:25 -------- d-----w- c:\documents and settings\Owner\Application Data\PlayPond
2010-11-03 14:37 . 2009-06-30 14:37 28552 ----a-w- c:\windows\system32\drivers\pavboot.sys
2010-11-03 14:35 . 2010-11-03 14:35 -------- d-----w- c:\program files\Panda Security
2010-10-29 02:13 . 2010-10-29 02:14 -------- d-----w- c:\program files\Mystery Legends - The Phantom of the Opera Collector's Edition
2010-10-20 14:56 . 2010-10-20 14:56 -------- d-----w- c:\program files\Microsoft Silverlight
2010-10-18 22:46 . 2010-10-18 22:46 -------- d-----w- C:\Color
2010-10-18 22:46 . 2010-10-18 22:46 -------- d-----w- C:\Custom
2010-10-18 22:45 . 2010-10-18 22:45 -------- d-----w- C:\Fontnav
2010-10-18 22:45 . 2010-10-18 22:45 -------- d-----w- C:\Macros
2010-10-18 22:45 . 2010-10-18 22:45 -------- d-----w- C:\Queries
2010-10-18 22:45 . 2010-10-18 22:46 -------- d-----w- C:\Config
2010-10-18 22:45 . 2010-10-18 22:45 -------- d-----w- C:\XML
2010-10-18 22:44 . 2010-10-18 22:45 -------- d-----w- C:\Template
2010-10-18 22:44 . 2010-10-18 22:46 -------- d-----w- C:\Filters
2010-10-18 22:44 . 2010-10-18 22:45 -------- d-----w- C:\Chart Support Files
2010-10-18 22:44 . 2010-10-18 22:45 -------- d-----w- C:\Graphics
2010-10-18 22:44 . 2010-11-03 15:24 -------- d-----w- C:\Programs
2010-10-18 22:44 . 2010-10-18 22:45 -------- d-----w- C:\Shared
2010-10-18 20:20 . 2010-11-10 12:49 -------- d-----w- c:\documents and settings\All Users\Application Data\WinZip
2010-10-15 21:10 . 2010-10-15 21:10 -------- d-----w- c:\program files\iPod
2010-10-15 21:09 . 2010-10-15 21:11 -------- d-----w- c:\program files\iTunes
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin7.dll
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin6.dll
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin5.dll
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin4.dll
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin3.dll
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin2.dll
2010-10-15 21:03 . 2010-10-15 21:03 159744 ----a-w- c:\program files\Internet Explorer\PLUGINS\npqtplugin.dll
2010-10-15 21:02 . 2010-10-15 21:03 -------- d-----w- c:\program files\QuickTime
2010-10-15 20:58 . 2010-10-15 20:58 -------- d-----w- c:\program files\Bonjour
2010-10-13 01:44 . 2010-09-18 06:53 974848 -c----w- c:\windows\system32\dllcache\mfc42.dll
2010-10-13 01:44 . 2010-08-23 16:12 617472 -c----w- c:\windows\system32\dllcache\comctl32.dll
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2010-10-18 22:48 . 2010-09-16 00:29 2516 --sha-w- c:\documents and settings\All Users\Application Data\KGyGaAvL.sys
2010-10-18 22:48 . 2010-09-16 00:29 88 --sh--r- c:\documents and settings\All Users\Application Data\CFD22FE827.sys
2010-09-18 16:23 . 2003-07-16 20:33 974848 ----a-w- c:\windows\system32\mfc42u.dll
2010-09-18 06:53 . 2003-07-16 20:33 974848 ----a-w- c:\windows\system32\mfc42.dll
2010-09-18 06:53 . 2003-07-16 20:33 954368 ----a-w- c:\windows\system32\mfc40.dll
2010-09-18 06:53 . 2003-07-16 20:33 953856 ----a-w- c:\windows\system32\mfc40u.dll
2010-09-15 08:50 . 2010-09-22 15:12 472808 ----a-w- c:\windows\system32\deployJava1.dll
2010-09-15 06:29 . 2010-02-18 23:20 73728 ----a-w- c:\windows\system32\javacpl.cpl
2010-09-10 05:58 . 2006-06-23 16:33 916480 ----a-w- c:\windows\system32\wininet.dll
2010-09-10 05:58 . 2003-07-16 20:32 43520 ----a-w- c:\windows\system32\licmgr10.dll
2010-09-10 05:58 . 2003-07-16 20:30 1469440 ----a-w- c:\windows\system32\inetcpl.cpl
2010-09-08 15:17 . 2010-09-08 15:17 94208 ----a-w- c:\windows\system32\QuickTimeVR.qtx
2010-09-08 15:17 . 2010-09-08 15:17 69632 ----a-w- c:\windows\system32\QuickTime.qts
2010-09-01 11:51 . 2003-07-16 20:24 285824 ----a-w- c:\windows\system32\atmfd.dll
2010-08-31 13:42 . 2003-07-16 20:51 1852800 ----a-w- c:\windows\system32\win32k.sys
2010-08-27 08:02 . 2003-07-16 20:47 119808 ----a-w- c:\windows\system32\t2embed.dll
2010-08-27 05:57 . 2003-07-16 20:46 99840 ----a-w- c:\windows\system32\srvsvc.dll
2010-08-26 13:39 . 2003-07-16 20:46 357248 ----a-w- c:\windows\system32\drivers\srv.sys
2010-08-26 12:52 . 2009-04-16 22:30 5120 ----a-w- c:\windows\system32\xpsp4res.dll
2010-08-23 16:12 . 2003-07-16 20:25 617472 ----a-w- c:\windows\system32\comctl32.dll
2010-08-17 13:17 . 2005-06-10 23:55 58880 ----a-w- c:\windows\system32\spoolsv.exe
2010-08-16 08:45 . 2004-03-06 02:16 590848 ----a-w- c:\windows\system32\rpcrt4.dll
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"BCMSMMSG"="BCMSMMSG.exe" [2003-08-29 122880]
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\winlogon\notify\GoToAssist]
2008-03-14 01:51 10536 ----a-w- c:\program files\Citrix\GoToAssist\508\g2awinlogon.dll
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\SymEFA.sys]
@="FSFilter Activity Monitor"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\Wdf01000.sys]
@="Driver"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\WudfSvc]
@="Service"
HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\DriverCure
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile]
"EnableFirewall"= 0 (0x0)
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"c:\\Program Files\\Sony\\Station\\LaunchPad\\LaunchPad.exe"=
"c:\\Program Files\\Kodak\\Kodak EasyShare software\\bin\\EasyShare.exe"=
"c:\\Program Files\\AIM6\\aim6.exe"=
"c:\\Program Files\\Common Files\\AOL\\Loader\\aolload.exe"=
"c:\\Program Files\\Bonjour\\mDNSResponder.exe"=
"c:\\Program Files\\iTunes\\iTunes.exe"=
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"1525:TCP"= 1525:TCP:Akamai NetSession Interface
"5000:UDP"= 5000:UDP:Akamai NetSession Interface
R0 pavboot;pavboot;c:\windows\system32\drivers\pavboot.sys [11/3/2010 9:37 AM 28552]
R0 SymEFA;Symantec Extended File Attributes;c:\windows\system32\drivers\N360\0308000.029\SymEFA.sys [2/25/2010 2:09 PM 310320]
R1 BHDrvx86;Symantec Heuristics Driver;c:\windows\system32\drivers\N360\0308000.029\BHDrvx86.sys [2/25/2010 2:09 PM 259632]
R1 ccHP;Symantec Hash Provider;c:\windows\system32\drivers\N360\0308000.029\cchpx86.sys [2/25/2010 2:09 PM 482432]
R1 IDSxpx86;IDSxpx86;c:\documents and settings\All Users\Application Data\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\Norton\Definitions\IPSDefs\20101109.001\IDSXpx86.sys [10/19/2010 3:36 PM 341880]
R2 N360;Norton Security Suite;c:\program files\Norton Security Suite\Engine\3.8.0.41\ccSvcHst.exe [2/25/2010 2:09 PM 117640]
R2 Viewpoint Manager Service;Viewpoint Manager Service;c:\program files\Viewpoint\Common\ViewpointService.exe [6/16/2009 8:16 PM 24652]
R3 EraserUtilRebootDrv;EraserUtilRebootDrv;c:\program files\Common Files\Symantec Shared\EENGINE\EraserUtilRebootDrv.sys [11/8/2010 10:35 AM 102448]
S3 EraserUtilDrvI9;EraserUtilDrvI9;\??\c:\program files\Common Files\Symantec Shared\EENGINE\EraserUtilDrvI9.sys --> c:\program files\Common Files\Symantec Shared\EENGINE\EraserUtilDrvI9.sys [?]
S3 MEMSWEEP2;MEMSWEEP2;\??\c:\windows\system32\19.tmp --> c:\windows\system32\19.tmp [?]
--- Other Services/Drivers In Memory ---
*NewlyCreated* - KLMD25
*Deregistered* - klmd25
*Deregistered* - uphcleanhlp
.
Contents of the 'Scheduled Tasks' folder
2010-11-05 c:\windows\Tasks\AppleSoftwareUpdate.job
- c:\program files\Apple Software Update\SoftwareUpdate.exe [2009-10-22 15:50]
.
.
------- Supplementary Scan -------
.
uStart Page = hxxp://www.comcast.net/
uSearchMigratedDefaultURL = hxxp://www.google.com/search?q={searchTerms}&sourceid=ie7&rls=com.microsoft:en-US&ie=utf8&oe=utf8
uInternet Connection Wizard,ShellNext = iexplore
uInternet Settings,ProxyOverride = *.local
IE: E&xport to Microsoft Excel - c:\progra~1\MICROS~4\Office12\EXCEL.EXE/3000
IE: Google Sidewiki... - c:\program files\Google\Google Toolbar\Component\GoogleToolbarDynamic_mui_en_89D8574934B26AC4.dll/cmsidewiki.html
IE: Open with WordPerfect - c:\program files\Corel\WordPerfect Office X5\Programs\WPLauncher.hta
Trusted Zone: internet
Trusted Zone: mcafee.com
DPF: {924B4927-D3BA-41EA-9F7E-8A89194AB3AC} - hxxp://panda-plugin.disney.go.com/plugin/win32/p3dactivex.cab
.
- - - - ORPHANS REMOVED - - - -
WebBrowser-{604BC32A-9680-40D1-9AC6-E06B23A1BA4C} - (no file)
WebBrowser-{D4027C7F-154A-4066-A1AD-4243D8127440} - (no file)
HKCU-Run-Aim6 - (no file)
HKLM-Run-MSN Toolbar - c:\program files\MSN Toolbar\Platform\4.0.0379.0\mswinext.exe
SafeBoot-WudfPf
SafeBoot-WudfRd
SafeBoot-MCODS
**************************************************************************
catchme 0.3.1398 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2010-11-11 10:34
Windows 5.1.2600 Service Pack 3 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
[HKEY_LOCAL_MACHINE\System\ControlSet002\Services\N360]
"ImagePath"="\"c:\program files\Norton Security Suite\Engine\3.8.0.41\ccSvcHst.exe\" /s \"N360\" /m \"c:\program files\Norton Security Suite\Engine\3.8.0.41\diMaster.dll\" /prefetch:1"
[HKEY_LOCAL_MACHINE\System\ControlSet002\Services\MEMSWEEP2]
"ImagePath"="\??\c:\windows\system32\19.tmp"
.
--------------------- LOCKED REGISTRY KEYS ---------------------
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}]
@Denied: (A 2) (Everyone)
@="FlashBroker"
"LocalizedString"="@c:\\WINDOWS\\system32\\Macromed\\Flash\\FlashUtil10k_ActiveX.exe,-101"
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\Elevation]
"Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\LocalServer32]
@="c:\\WINDOWS\\system32\\Macromed\\Flash\\FlashUtil10k_ActiveX.exe"
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}]
@Denied: (A 2) (Everyone)
@="IFlashBroker4"
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\ProxyStubClsid32]
@="{00020424-0000-0000-C000-000000000046}"
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
"Version"="1.0"
.
--------------------- DLLs Loaded Under Running Processes ---------------------
- - - - - - - > 'winlogon.exe'(888)
c:\program files\Citrix\GoToAssist\508\G2AWinLogon.dll
.
Completion time: 2010-11-11 10:38:44
ComboFix-quarantined-files.txt 2010-11-11 15:38
Pre-Run: 16,581,730,304 bytes free
Post-Run: 16,576,548,864 bytes free
WindowsXP-KB310994-SP2-Home-BootDisk-ENU.exe
[boot loader]
timeout=2
default=multi(0)disk(0)rdisk(0)partition(1)\WINDOWS
[operating systems]
c:\cmdcons\BOOTSECT.DAT="Microsoft Windows Recovery Console" /cmdcons
UnsupportedDebug="do not select this" /debug
multi(0)disk(0)rdisk(0)partition(1)\WINDOWS="Microsoft Windows XP Home Edition" /fastdetect /NoExecute=OptIn
multi(0)disk(0)rdisk(0)partition(2)\WINDOWS="Microsoft Windows XP Home Edition" /fastdetect
- - End Of File - - 704AA5944A8797ADFB96A16F1DD11132
Download ComboFix here :
* IMPORTANT !!! Save ComboFix.exe to your Desktop
- Disable your AntiVirus and AntiSpyware applications, usually via a right click on the System Tray icon. They may otherwise interfere with our tools. Here is a guide on how to disable them
Click me - Double click on ComboFix.exe & follow the prompts.
- As part of it's process, ComboFix will check to see if the Microsoft Windows Recovery Console is installed. With malware infections being as they are today, it's strongly recommended to have this pre-installed on your machine before doing any malware removal. It will allow you to boot up into a special recovery/repair mode that will allow us to more easily help you should your computer have a problem after an attempted removal of malware.
- Follow the prompts to allow ComboFix to download and install the Microsoft Windows Recovery Console, and when prompted, agree to the End-User License Agreement to install the Microsoft Windows Recovery Console.
**Please note: If the Microsoft Windows Recovery Console is already installed, ComboFix will continue it's malware removal procedures.
Once the Microsoft Windows Recovery Console is installed using ComboFix, you should see the following message:
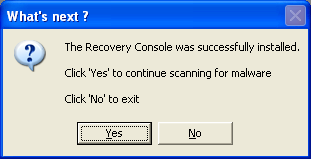
Click on Yes, to continue scanning for malware.
When finished, it shall produce a log for you. Please include the C:\ComboFix.txt log in your next reply.
- Disable your AntiVirus and AntiSpyware applications, usually via a right click on the System Tray icon. They may otherwise interfere with our tools. Here is a guide on how to disable them
-
Sorry about the confusion!
2010/11/10 23:43:14.0515 TDSS rootkit removing tool 2.4.7.0 Nov 8 2010 10:52:22
2010/11/10 23:43:14.0515 ================================================================================
2010/11/10 23:43:14.0515 SystemInfo:
2010/11/10 23:43:14.0515
2010/11/10 23:43:14.0515 OS Version: 5.1.2600 ServicePack: 3.0
2010/11/10 23:43:14.0515 Product type: Workstation
2010/11/10 23:43:14.0515 ComputerName: BIGDADDYCVK
2010/11/10 23:43:14.0515 UserName: Owner
2010/11/10 23:43:14.0515 Windows directory: C:\WINDOWS
2010/11/10 23:43:14.0515 System windows directory: C:\WINDOWS
2010/11/10 23:43:14.0515 Processor architecture: Intel x86
2010/11/10 23:43:14.0515 Number of processors: 1
2010/11/10 23:43:14.0515 Page size: 0x1000
2010/11/10 23:43:14.0515 Boot type: Normal boot
2010/11/10 23:43:14.0515 ================================================================================
2010/11/10 23:43:16.0453 Initialize success
2010/11/10 23:43:24.0406 ================================================================================
2010/11/10 23:43:24.0406 Scan started
2010/11/10 23:43:24.0406 Mode: Manual;
2010/11/10 23:43:24.0406 ================================================================================
2010/11/10 23:43:26.0687 ACPI (8fd99680a539792a30e97944fdaecf17) C:\WINDOWS\system32\DRIVERS\ACPI.sys
2010/11/10 23:43:27.0156 ACPIEC (9859c0f6936e723e4892d7141b1327d5) C:\WINDOWS\system32\drivers\ACPIEC.sys
2010/11/10 23:43:28.0062 aeaudio (11c04b17ed2abbb4833694bcd644ac90) C:\WINDOWS\system32\drivers\aeaudio.sys
2010/11/10 23:43:28.0562 aec (8bed39e3c35d6a489438b8141717a557) C:\WINDOWS\system32\drivers\aec.sys
2010/11/10 23:43:29.0156 Afc (a7b8a3a79d35215d798a300df49ed23f) C:\WINDOWS\system32\drivers\Afc.sys
2010/11/10 23:43:29.0640 AFD (7e775010ef291da96ad17ca4b17137d7) C:\WINDOWS\System32\drivers\afd.sys
2010/11/10 23:43:33.0968 AsyncMac (b153affac761e7f5fcfa822b9c4e97bc) C:\WINDOWS\system32\DRIVERS\asyncmac.sys
2010/11/10 23:43:34.0765 atapi (9f3a2f5aa6875c72bf062c712cfa2674) C:\WINDOWS\system32\DRIVERS\atapi.sys
2010/11/10 23:43:35.0921 Atmarpc (9916c1225104ba14794209cfa8012159) C:\WINDOWS\system32\DRIVERS\atmarpc.sys
2010/11/10 23:43:36.0625 audstub (d9f724aa26c010a217c97606b160ed68) C:\WINDOWS\system32\DRIVERS\audstub.sys
2010/11/10 23:43:37.0328 bcm4sbxp (b60f57b4d9cdbc663cc03eb8af7ec34e) C:\WINDOWS\system32\DRIVERS\bcm4sbxp.sys
2010/11/10 23:43:38.0656 BCMModem (41347688046d49cde0f6d138a534f73d) C:\WINDOWS\system32\DRIVERS\BCMSM.sys
2010/11/10 23:43:39.0843 Beep (df012c2853281ce2bf536e8de871c8c1) C:\WINDOWS\system32\drivers\Beep.sys
2010/11/10 23:43:40.0781 BHDrvx86 (76154fa6a742c613b44bb636b1a7c057) C:\WINDOWS\System32\Drivers\N360\0308000.029\BHDrvx86.sys
2010/11/10 23:43:41.0406 BVRPMPR5 (248dfa5762dde38dfddbbd44149e9d7a) C:\WINDOWS\system32\drivers\BVRPMPR5.SYS
2010/11/10 23:43:41.0859 cbidf2k (90a673fc8e12a79afbed2576f6a7aaf9) C:\WINDOWS\system32\drivers\cbidf2k.sys
2010/11/10 23:43:42.0718 ccHP (8973ff34b83572d867b5b928905ad5ac) C:\WINDOWS\System32\Drivers\N360\0308000.029\ccHPx86.sys
2010/11/10 23:43:43.0531 Cdaudio (c1b486a7658353d33a10cc15211a873b) C:\WINDOWS\system32\drivers\Cdaudio.sys
2010/11/10 23:43:44.0281 Cdfs (c885b02847f5d2fd45a24e219ed93b32) C:\WINDOWS\system32\drivers\Cdfs.sys
2010/11/10 23:43:44.0812 Cdrom (4b0a100eaf5c49ef3cca8c641431eacc) C:\WINDOWS\system32\DRIVERS\cdrom.sys
2010/11/10 23:43:47.0109 Disk (044452051f3e02e7963599fc8f4f3e25) C:\WINDOWS\system32\DRIVERS\disk.sys
2010/11/10 23:43:47.0906 dmboot (d992fe1274bde0f84ad826acae022a41) C:\WINDOWS\system32\drivers\dmboot.sys
2010/11/10 23:43:48.0687 dmio (7c824cf7bbde77d95c08005717a95f6f) C:\WINDOWS\system32\drivers\dmio.sys
2010/11/10 23:43:49.0281 dmload (e9317282a63ca4d188c0df5e09c6ac5f) C:\WINDOWS\system32\drivers\dmload.sys
2010/11/10 23:43:49.0781 DMusic (8a208dfcf89792a484e76c40e5f50b45) C:\WINDOWS\system32\drivers\DMusic.sys
2010/11/10 23:43:50.0640 drmkaud (8f5fcff8e8848afac920905fbd9d33c8) C:\WINDOWS\system32\drivers\drmkaud.sys
2010/11/10 23:43:51.0109 eeCtrl (089296aedb9b72b4916ac959752bdc89) C:\Program Files\Common Files\Symantec Shared\EENGINE\eeCtrl.sys
2010/11/10 23:43:51.0343 EraserUtilRebootDrv (850259334652d392e33ee3412562e583) C:\Program Files\Common Files\Symantec Shared\EENGINE\EraserUtilRebootDrv.sys
2010/11/10 23:43:51.0859 Fastfat (38d332a6d56af32635675f132548343e) C:\WINDOWS\system32\drivers\Fastfat.sys
2010/11/10 23:43:52.0562 Fdc (92cdd60b6730b9f50f6a1a0c1f8cdc81) C:\WINDOWS\system32\DRIVERS\fdc.sys
2010/11/10 23:43:53.0046 Fips (d45926117eb9fa946a6af572fbe1caa3) C:\WINDOWS\system32\drivers\Fips.sys
2010/11/10 23:43:53.0562 Flpydisk (9d27e7b80bfcdf1cdd9b555862d5e7f0) C:\WINDOWS\system32\DRIVERS\flpydisk.sys
2010/11/10 23:43:54.0046 FltMgr (b2cf4b0786f8212cb92ed2b50c6db6b0) C:\WINDOWS\system32\drivers\fltmgr.sys
2010/11/10 23:43:54.0718 Fs_Rec (3e1e2bd4f39b0e2b7dc4f4d2bcc2779a) C:\WINDOWS\system32\drivers\Fs_Rec.sys
2010/11/10 23:43:55.0562 Ftdisk (6ac26732762483366c3969c9e4d2259d) C:\WINDOWS\system32\DRIVERS\ftdisk.sys
2010/11/10 23:43:56.0250 GEARAspiWDM (8182ff89c65e4d38b2de4bb0fb18564e) C:\WINDOWS\system32\DRIVERS\GEARAspiWDM.sys
2010/11/10 23:43:56.0937 Gpc (0a02c63c8b144bd8c86b103dee7c86a2) C:\WINDOWS\system32\DRIVERS\msgpc.sys
2010/11/10 23:43:58.0000 HTTP (f80a415ef82cd06ffaf0d971528ead38) C:\WINDOWS\system32\Drivers\HTTP.sys
2010/11/10 23:43:59.0281 i8042prt (4a0b06aa8943c1e332520f7440c0aa30) C:\WINDOWS\system32\DRIVERS\i8042prt.sys
2010/11/10 23:43:59.0812 ialm (b076eb745ec3c669d4ae953225366f1d) C:\WINDOWS\system32\DRIVERS\ialmnt5.sys
2010/11/10 23:44:00.0484 IDSxpx86 (74e8463447101ecf0165ddc7e5168b7e) C:\Documents and Settings\All Users\Application Data\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\Norton\Definitions\ipsdefs\20101109.001\IDSxpx86.sys
2010/11/10 23:44:01.0000 Imapi (083a052659f5310dd8b6a6cb05edcf8e) C:\WINDOWS\system32\DRIVERS\imapi.sys
2010/11/10 23:44:01.0984 IntelIde (b5466a9250342a7aa0cd1fba13420678) C:\WINDOWS\system32\DRIVERS\intelide.sys
2010/11/10 23:44:02.0937 intelppm (8c953733d8f36eb2133f5bb58808b66b) C:\WINDOWS\system32\DRIVERS\intelppm.sys
2010/11/10 23:44:03.0656 ip6fw (3bb22519a194418d5fec05d800a19ad0) C:\WINDOWS\system32\drivers\ip6fw.sys
2010/11/10 23:44:04.0250 IpFilterDriver (731f22ba402ee4b62748adaf6363c182) C:\WINDOWS\system32\DRIVERS\ipfltdrv.sys
2010/11/10 23:44:04.0687 IpInIp (b87ab476dcf76e72010632b5550955f5) C:\WINDOWS\system32\DRIVERS\ipinip.sys
2010/11/10 23:44:05.0328 IpNat (cc748ea12c6effde940ee98098bf96bb) C:\WINDOWS\system32\DRIVERS\ipnat.sys
2010/11/10 23:44:06.0062 IPSec (23c74d75e36e7158768dd63d92789a91) C:\WINDOWS\system32\DRIVERS\ipsec.sys
2010/11/10 23:44:06.0750 IRENUM (c93c9ff7b04d772627a3646d89f7bf89) C:\WINDOWS\system32\DRIVERS\irenum.sys
2010/11/10 23:44:07.0437 isapnp (05a299ec56e52649b1cf2fc52d20f2d7) C:\WINDOWS\system32\DRIVERS\isapnp.sys
2010/11/10 23:44:07.0828 Kbdclass (463c1ec80cd17420a542b7f36a36f128) C:\WINDOWS\system32\DRIVERS\kbdclass.sys
2010/11/10 23:44:08.0515 kmixer (692bcf44383d056aed41b045a323d378) C:\WINDOWS\system32\drivers\kmixer.sys
2010/11/10 23:44:08.0968 KSecDD (b467646c54cc746128904e1654c750c1) C:\WINDOWS\system32\drivers\KSecDD.sys
2010/11/10 23:44:10.0281 mnmdd (4ae068242760a1fb6e1a44bf4e16afa6) C:\WINDOWS\system32\drivers\mnmdd.sys
2010/11/10 23:44:10.0843 Modem (dfcbad3cec1c5f964962ae10e0bcc8e1) C:\WINDOWS\system32\drivers\Modem.sys
2010/11/10 23:44:11.0250 MODEMCSA (1992e0d143b09653ab0f9c5e04b0fd65) C:\WINDOWS\system32\drivers\MODEMCSA.sys
2010/11/10 23:44:11.0875 Mouclass (35c9e97194c8cfb8430125f8dbc34d04) C:\WINDOWS\system32\DRIVERS\mouclass.sys
2010/11/10 23:44:12.0390 MountMgr (a80b9a0bad1b73637dbcbba7df72d3fd) C:\WINDOWS\system32\drivers\MountMgr.sys
2010/11/10 23:44:13.0140 MRxDAV (11d42bb6206f33fbb3ba0288d3ef81bd) C:\WINDOWS\system32\DRIVERS\mrxdav.sys
2010/11/10 23:44:13.0718 MRxSmb (f3aefb11abc521122b67095044169e98) C:\WINDOWS\system32\DRIVERS\mrxsmb.sys
2010/11/10 23:44:14.0250 Msfs (c941ea2454ba8350021d774daf0f1027) C:\WINDOWS\system32\drivers\Msfs.sys
2010/11/10 23:44:14.0640 MSKSSRV (d1575e71568f4d9e14ca56b7b0453bf1) C:\WINDOWS\system32\drivers\MSKSSRV.sys
2010/11/10 23:44:15.0140 MSPCLOCK (325bb26842fc7ccc1fcce2c457317f3e) C:\WINDOWS\system32\drivers\MSPCLOCK.sys
2010/11/10 23:44:15.0671 MSPQM (bad59648ba099da4a17680b39730cb3d) C:\WINDOWS\system32\drivers\MSPQM.sys
2010/11/10 23:44:16.0312 mssmbios (af5f4f3f14a8ea2c26de30f7a1e17136) C:\WINDOWS\system32\DRIVERS\mssmbios.sys
2010/11/10 23:44:17.0156 Mup (2f625d11385b1a94360bfc70aaefdee1) C:\WINDOWS\system32\drivers\Mup.sys
2010/11/10 23:44:17.0531 NAVENG (49d802531e5984cf1fe028c6c129b9d8) C:\Documents and Settings\All Users\Application Data\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\Norton\Definitions\VirusDefs\20101110.021\NAVENG.SYS
2010/11/10 23:44:18.0312 NAVEX15 (158676a5758c1fa519563b3e72fbf256) C:\Documents and Settings\All Users\Application Data\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\Norton\Definitions\VirusDefs\20101110.021\NAVEX15.SYS
2010/11/10 23:44:18.0843 NDIS (1df7f42665c94b825322fae71721130d) C:\WINDOWS\system32\drivers\NDIS.sys
2010/11/10 23:44:19.0296 NdisTapi (1ab3d00c991ab086e69db84b6c0ed78f) C:\WINDOWS\system32\DRIVERS\ndistapi.sys
2010/11/10 23:44:19.0781 Ndisuio (f927a4434c5028758a842943ef1a3849) C:\WINDOWS\system32\DRIVERS\ndisuio.sys
2010/11/10 23:44:20.0281 NdisWan (edc1531a49c80614b2cfda43ca8659ab) C:\WINDOWS\system32\DRIVERS\ndiswan.sys
2010/11/10 23:44:20.0812 NDProxy (6215023940cfd3702b46abc304e1d45a) C:\WINDOWS\system32\drivers\NDProxy.sys
2010/11/10 23:44:21.0312 NetBIOS (5d81cf9a2f1a3a756b66cf684911cdf0) C:\WINDOWS\system32\DRIVERS\netbios.sys
2010/11/10 23:44:21.0765 NetBT (74b2b2f5bea5e9a3dc021d685551bd3d) C:\WINDOWS\system32\DRIVERS\netbt.sys
2010/11/10 23:44:22.0328 Npfs (3182d64ae053d6fb034f44b6def8034a) C:\WINDOWS\system32\drivers\Npfs.sys
2010/11/10 23:44:22.0968 Ntfs (78a08dd6a8d65e697c18e1db01c5cdca) C:\WINDOWS\system32\drivers\Ntfs.sys
2010/11/10 23:44:23.0546 Null (73c1e1f395918bc2c6dd67af7591a3ad) C:\WINDOWS\system32\drivers\Null.sys
2010/11/10 23:44:24.0093 NwlnkFlt (b305f3fad35083837ef46a0bbce2fc57) C:\WINDOWS\system32\DRIVERS\nwlnkflt.sys
2010/11/10 23:44:24.0546 NwlnkFwd (c99b3415198d1aab7227f2c88fd664b9) C:\WINDOWS\system32\DRIVERS\nwlnkfwd.sys
2010/11/10 23:44:25.0203 OMCI (cec7e2c6c1fa00c7ab2f5434f848ae51) C:\WINDOWS\SYSTEM32\DRIVERS\OMCI.SYS
2010/11/10 23:44:25.0640 Parport (5575faf8f97ce5e713d108c2a58d7c7c) C:\WINDOWS\system32\DRIVERS\parport.sys
2010/11/10 23:44:26.0281 PartMgr (beb3ba25197665d82ec7065b724171c6) C:\WINDOWS\system32\drivers\PartMgr.sys
2010/11/10 23:44:26.0687 ParVdm (70e98b3fd8e963a6a46a2e6247e0bea1) C:\WINDOWS\system32\drivers\ParVdm.sys
2010/11/10 23:44:27.0203 pavboot (3adb8bd6154a3ef87496e8fce9c22493) C:\WINDOWS\system32\drivers\pavboot.sys
2010/11/10 23:44:27.0906 PCI (a219903ccf74233761d92bef471a07b1) C:\WINDOWS\system32\DRIVERS\pci.sys
2010/11/10 23:44:28.0796 PCIIde (ccf5f451bb1a5a2a522a76e670000ff0) C:\WINDOWS\system32\DRIVERS\pciide.sys
2010/11/10 23:44:29.0265 Pcmcia (9e89ef60e9ee05e3f2eef2da7397f1c1) C:\WINDOWS\system32\drivers\Pcmcia.sys
2010/11/10 23:44:31.0656 PptpMiniport (efeec01b1d3cf84f16ddd24d9d9d8f99) C:\WINDOWS\system32\DRIVERS\raspptp.sys
2010/11/10 23:44:32.0156 Processor (a32bebaf723557681bfc6bd93e98bd26) C:\WINDOWS\system32\DRIVERS\processr.sys
2010/11/10 23:44:32.0671 PSched (09298ec810b07e5d582cb3a3f9255424) C:\WINDOWS\system32\DRIVERS\psched.sys
2010/11/10 23:44:33.0156 Ptilink (80d317bd1c3dbc5d4fe7b1678c60cadd) C:\WINDOWS\system32\DRIVERS\ptilink.sys
2010/11/10 23:44:33.0640 PxHelp20 (d86b4a68565e444d76457f14172c875a) C:\WINDOWS\system32\Drivers\PxHelp20.sys
2010/11/10 23:44:35.0671 RasAcd (fe0d99d6f31e4fad8159f690d68ded9c) C:\WINDOWS\system32\DRIVERS\rasacd.sys
2010/11/10 23:44:36.0078 Rasl2tp (11b4a627bc9614b885c4969bfa5ff8a6) C:\WINDOWS\system32\DRIVERS\rasl2tp.sys
2010/11/10 23:44:36.0593 RasPppoe (5bc962f2654137c9909c3d4603587dee) C:\WINDOWS\system32\DRIVERS\raspppoe.sys
2010/11/10 23:44:37.0390 Raspti (fdbb1d60066fcfbb7452fd8f9829b242) C:\WINDOWS\system32\DRIVERS\raspti.sys
2010/11/10 23:44:37.0890 Rdbss (7ad224ad1a1437fe28d89cf22b17780a) C:\WINDOWS\system32\DRIVERS\rdbss.sys
2010/11/10 23:44:38.0359 RDPCDD (4912d5b403614ce99c28420f75353332) C:\WINDOWS\system32\DRIVERS\RDPCDD.sys
2010/11/10 23:44:39.0218 RDPWD (6728e45b66f93c08f11de2e316fc70dd) C:\WINDOWS\system32\drivers\RDPWD.sys
2010/11/10 23:44:39.0843 redbook (f828dd7e1419b6653894a8f97a0094c5) C:\WINDOWS\system32\DRIVERS\redbook.sys
2010/11/10 23:44:40.0250 ROOTMODEM (d8b0b4ade32574b2d9c5cc34dc0dbbe7) C:\WINDOWS\system32\Drivers\RootMdm.sys
2010/11/10 23:44:40.0796 Secdrv (90a3935d05b494a5a39d37e71f09a677) C:\WINDOWS\system32\DRIVERS\secdrv.sys
2010/11/10 23:44:41.0281 serenum (0f29512ccd6bead730039fb4bd2c85ce) C:\WINDOWS\system32\DRIVERS\serenum.sys
2010/11/10 23:44:41.0781 Serial (cca207a8896d4c6a0c9ce29a4ae411a7) C:\WINDOWS\system32\DRIVERS\serial.sys
2010/11/10 23:44:42.0343 Sfloppy (8e6b8c671615d126fdc553d1e2de5562) C:\WINDOWS\system32\drivers\Sfloppy.sys
2010/11/10 23:44:43.0328 smwdm (31fd0707c7dbe715234f2823b27214fe) C:\WINDOWS\system32\drivers\smwdm.sys
2010/11/10 23:44:44.0281 splitter (ab8b92451ecb048a4d1de7c3ffcb4a9f) C:\WINDOWS\system32\drivers\splitter.sys
2010/11/10 23:44:44.0687 sr (76bb022c2fb6902fd5bdd4f78fc13a5d) C:\WINDOWS\system32\DRIVERS\sr.sys
2010/11/10 23:44:45.0281 SRTSP (e81f6caeab9ad5732e94c07c97866aa2) C:\WINDOWS\System32\Drivers\N360\0308000.029\SRTSP.SYS
2010/11/10 23:44:45.0890 SRTSPX (e28de499d942b08058bffac69d4122b6) C:\WINDOWS\system32\drivers\N360\0308000.029\SRTSPX.SYS
2010/11/10 23:44:46.0500 Srv (0f6aefad3641a657e18081f52d0c15af) C:\WINDOWS\system32\DRIVERS\srv.sys
2010/11/10 23:44:47.0046 swenum (3941d127aef12e93addf6fe6ee027e0f) C:\WINDOWS\system32\DRIVERS\swenum.sys
2010/11/10 23:44:47.0609 swmidi (8ce882bcc6cf8a62f2b2323d95cb3d01) C:\WINDOWS\system32\drivers\swmidi.sys
2010/11/10 23:44:48.0828 SymEFA (d0885f6e24259a6c65e68d6ad749910a) C:\WINDOWS\system32\drivers\N360\0308000.029\SYMEFA.SYS
2010/11/10 23:44:49.0500 SymEvent (a54ff04bd6e75dc4d8cb6f3e352635e0) C:\WINDOWS\system32\Drivers\SYMEVENT.SYS
2010/11/10 23:44:50.0406 SYMFW (1e825026436c4eac3e1a11d1e9c33f2c) C:\WINDOWS\System32\Drivers\N360\0308000.029\SYMFW.SYS
2010/11/10 23:44:50.0921 SYMIDS (7a20b7d774ef0f16cf81b898bfeca772) C:\WINDOWS\System32\Drivers\N360\0308000.029\SYMIDS.SYS
2010/11/10 23:44:51.0312 SymIM (c6db9f873b09c63f5cb1de10c08bf6f9) C:\WINDOWS\system32\DRIVERS\SymIM.sys
2010/11/10 23:44:51.0390 SymIMMP (c6db9f873b09c63f5cb1de10c08bf6f9) C:\WINDOWS\system32\DRIVERS\SymIM.sys
2010/11/10 23:44:51.0890 SYMNDIS (5ab7d00ea6b7a6fcd5067c632ec6f039) C:\WINDOWS\System32\Drivers\N360\0308000.029\SYMNDIS.SYS
2010/11/10 23:44:52.0437 SYMTDI (e4fa8bbb96e314e9508865de1a767538) C:\WINDOWS\System32\Drivers\N360\0308000.029\SYMTDI.SYS
2010/11/10 23:44:53.0468 sysaudio (8b83f3ed0f1688b4958f77cd6d2bf290) C:\WINDOWS\system32\drivers\sysaudio.sys
2010/11/10 23:44:53.0984 Tcpip (9aefa14bd6b182d61e3119fa5f436d3d) C:\WINDOWS\system32\DRIVERS\tcpip.sys
2010/11/10 23:44:54.0468 TDPIPE (6471a66807f5e104e4885f5b67349397) C:\WINDOWS\system32\drivers\TDPIPE.sys
2010/11/10 23:44:54.0906 TDTCP (c56b6d0402371cf3700eb322ef3aaf61) C:\WINDOWS\system32\drivers\TDTCP.sys
2010/11/10 23:44:55.0390 TermDD (88155247177638048422893737429d9e) C:\WINDOWS\system32\DRIVERS\termdd.sys
2010/11/10 23:44:56.0250 Udfs (5787b80c2e3c5e2f56c2a233d91fa2c9) C:\WINDOWS\system32\drivers\Udfs.sys
2010/11/10 23:44:56.0890 UnlockerDriver5 (4847639d852763ee39415c929470f672) C:\Program Files\Unlocker\UnlockerDriver5.sys
2010/11/10 23:44:57.0609 Update (402ddc88356b1bac0ee3dd1580c76a31) C:\WINDOWS\system32\DRIVERS\update.sys
2010/11/10 23:44:58.0218 USBAAPL (4b8a9c16b6d9258ed99c512aecb8c555) C:\WINDOWS\system32\Drivers\usbaapl.sys
2010/11/10 23:44:58.0734 usbccgp (173f317ce0db8e21322e71b7e60a27e8) C:\WINDOWS\system32\DRIVERS\usbccgp.sys
2010/11/10 23:44:59.0218 usbehci (65dcf09d0e37d4c6b11b5b0b76d470a7) C:\WINDOWS\system32\DRIVERS\usbehci.sys
2010/11/10 23:44:59.0750 usbhub (1ab3cdde553b6e064d2e754efe20285c) C:\WINDOWS\system32\DRIVERS\usbhub.sys
2010/11/10 23:45:00.0234 usbprint (a717c8721046828520c9edf31288fc00) C:\WINDOWS\system32\DRIVERS\usbprint.sys
2010/11/10 23:45:01.0421 usbscan (a0b8cf9deb1184fbdd20784a58fa75d4) C:\WINDOWS\system32\DRIVERS\usbscan.sys
2010/11/10 23:45:01.0890 USBSTOR (a32426d9b14a089eaa1d922e0c5801a9) C:\WINDOWS\system32\DRIVERS\USBSTOR.SYS
2010/11/10 23:45:02.0406 usbuhci (26496f9dee2d787fc3e61ad54821ffe6) C:\WINDOWS\system32\DRIVERS\usbuhci.sys
2010/11/10 23:45:02.0875 VgaSave (0d3a8fafceacd8b7625cd549757a7df1) C:\WINDOWS\System32\drivers\vga.sys
2010/11/10 23:45:03.0531 VolSnap (4c8fcb5cc53aab716d810740fe59d025) C:\WINDOWS\system32\drivers\VolSnap.sys
2010/11/10 23:45:03.0984 Wanarp (e20b95baedb550f32dd489265c1da1f6) C:\WINDOWS\system32\DRIVERS\wanarp.sys
2010/11/10 23:45:04.0562 Wdf01000 (d918617b46457b9ac28027722e30f647) C:\WINDOWS\system32\DRIVERS\Wdf01000.sys
2010/11/10 23:45:05.0531 wdmaud (6768acf64b18196494413695f0c3a00f) C:\WINDOWS\system32\drivers\wdmaud.sys
2010/11/10 23:45:06.0015 WinDriver6 (097a8291df541f9b9af2c500797cdcaa) C:\WINDOWS\system32\drivers\windrvr6.sys
2010/11/10 23:45:06.0750 WinUSB (fd600b032e741eb6aab509fc630f7c42) C:\WINDOWS\system32\DRIVERS\WinUSB.sys
2010/11/10 23:45:07.0234 WpdUsb (cf4def1bf66f06964dc0d91844239104) C:\WINDOWS\system32\DRIVERS\wpdusb.sys
2010/11/10 23:45:07.0765 WudfPf (eaa6324f51214d2f6718977ec9ce0def) C:\WINDOWS\system32\DRIVERS\WudfPf.sys
2010/11/10 23:45:08.0562 {6080A529-897E-4629-A488-ABA0C29B635E} (61002db7b6efb5711685b9d79b8e8ce6) C:\WINDOWS\system32\drivers\ialmsbw.sys
-
I was told that there was spyware/malware on my computer by one of those companies that fix your computer over the Internet. I originally inquired because over the past few months, I've had to double/triple click on everything to get a response from the mouse, and the computer has been acting very slow at times. Thanks for your help.
don't attach the logs
Run OTL
- Under the Custom Scans/Fixes box at the bottom, paste in the following
:OTL
[2008/08/03 20:36:52 | 000,019,371 | ---- | C] () -- C:\Program Files\Common Files\kyfe._sy
[2008/08/03 20:36:52 | 000,016,947 | ---- | C] () -- C:\Documents and Settings\Owner\Local Settings\Application Data\miwod.dl
[2008/08/03 20:36:52 | 000,016,537 | ---- | C] () -- C:\Documents and Settings\Owner\Local Settings\Application Data\lexo.db
[2008/08/03 20:36:52 | 000,012,107 | ---- | C] () -- C:\Documents and Settings\Owner\Local Settings\Application Data\yruny.bin
[2008/08/03 20:36:51 | 000,014,258 | ---- | C] () -- C:\WINDOWS\wehoryzij.dll
[2008/08/03 20:36:51 | 000,013,255 | ---- | C] () -- C:\Documents and Settings\All Users\Application Data\ebilize.bin
[2008/08/03 20:36:51 | 000,012,333 | ---- | C] () -- C:\Documents and Settings\Owner\Application Data\wuketimas.vbs
[2008/08/03 20:36:51 | 000,011,242 | ---- | C] () -- C:\Documents and Settings\All Users\Application Data\acanyq._sy
[2008/08/03 20:36:50 | 000,017,363 | ---- | C] () -- C:\Documents and Settings\Owner\Local Settings\Application Data\wawidovu.dl
[2008/08/03 20:36:50 | 000,013,473 | ---- | C] () -- C:\Documents and Settings\Owner\Local Settings\Application Data\ulewocywev.sys
[2008/08/03 20:36:50 | 000,010,131 | ---- | C] () -- C:\Documents and Settings\Owner\Local Settings\Application Data\usefyl.db
[2008/08/03 10:24:23 | 000,000,128 | ---- | C] () -- C:\Documents and Settings\Owner\Local Settings\Application Data\fusioncache.dat
[2008/08/02 23:04:45 | 000,019,156 | ---- | C] () -- C:\Documents and Settings\All Users\Application Data\gufevenal.dat
[2008/08/02 23:04:45 | 000,019,015 | ---- | C] () -- C:\Documents and Settings\Owner\Local Settings\Application Data\pycydaceg.bin
[2008/08/02 23:04:45 | 000,018,018 | ---- | C] () -- C:\Program Files\Common Files\ihanuruma.dl
[2008/08/02 23:04:45 | 000,017,896 | ---- | C] () -- C:\Program Files\Common Files\ezale.com
[2008/08/02 23:04:45 | 000,015,547 | ---- | C] () -- C:\Documents and Settings\All Users\Application Data\xylisape._dl
[2008/08/02 23:04:45 | 000,015,428 | ---- | C] () -- C:\Program Files\Common Files\nyhakopeba.bat
[2008/08/02 23:04:45 | 000,014,060 | ---- | C] () -- C:\Documents and Settings\Owner\Local Settings\Application Data\tuquna._dl
[2008/08/02 23:04:45 | 000,013,901 | ---- | C] () -- C:\Program Files\Common Files\exiw.pif
[2008/08/02 23:04:45 | 000,013,851 | ---- | C] () -- C:\Documents and Settings\All Users\Application Data\ogoniniti.bin
[2008/08/02 23:04:45 | 000,013,676 | ---- | C] () -- C:\Program Files\Common Files\bywaki.dat
[2008/08/02 23:04:45 | 000,012,343 | ---- | C] () -- C:\Documents and Settings\Owner\Application Data\lydeviho.dl
[2008/08/02 23:04:45 | 000,011,929 | ---- | C] () -- C:\Documents and Settings\Owner\Application Data\vorinunif.com
[2008/08/02 23:04:45 | 000,011,322 | ---- | C] () -- C:\Program Files\Common Files\vemenem.com
[2008/08/02 23:04:45 | 000,010,444 | ---- | C] () -- C:\Documents and Settings\All Users\Application Data\mohexoredu.ban
[2008/03/31 14:18:54 | 000,000,000 | ---- | C] () -- C:\Program Files\temp01
[2008/07/29 13:59:43 | 000,000,000 | ---D | M] -- C:\Documents and Settings\All Users\Application Data\n7-89-o9-3r-4t-r9
[2008/08/02 23:04:45 | 000,010,013 | ---- | M] () -- C:\WINDOWS\conymyv.scr
[2008/08/02 23:04:45 | 000,013,021 | ---- | M] () -- C:\WINDOWS\aranade._sy
[2008/08/02 23:04:45 | 000,014,964 | ---- | M] () -- C:\WINDOWS\inupa._sy
[2008/08/02 23:04:45 | 000,013,676 | ---- | M] () -- C:\Program Files\Common Files\bywaki.dat
[2008/08/02 23:04:45 | 000,013,901 | ---- | M] () -- C:\Program Files\Common Files\exiw.pif
[2008/08/02 23:04:45 | 000,017,896 | ---- | M] () -- C:\Program Files\Common Files\ezale.com
[2008/08/02 23:04:45 | 000,018,018 | ---- | M] () -- C:\Program Files\Common Files\ihanuruma.dl
[2008/08/03 20:36:52 | 000,019,371 | ---- | M] () -- C:\Program Files\Common Files\kyfe._sy
[2008/08/02 23:04:45 | 000,015,428 | ---- | M] () -- C:\Program Files\Common Files\nyhakopeba.bat
[2008/08/02 23:04:45 | 000,011,322 | ---- | M] () -- C:\Program Files\Common Files\vemenem.com
[2008/07/24 20:01:48 | 000,000,000 | ---D | M] -- C:\Program Files\Coupons
:Services
:Reg
:Files
ipconfig /flushdns /c
%systemroot%\prefetch\*.*
:Commands
[purity]
[resethosts]
[emptytemp]
[EMPTYFLASH]
[CREATERESTOREPOINT]
[Reboot] - Then click the Run Fix button at the top
- Let the program run unhindered, reboot the PC when it is done
Please read carefully and follow these steps.
- Download TDSSKiller and save it to your Desktop.
- Extract its contents to your desktop.
- Once extracted, open the TDSSKiller folder and doubleclick on TDSSKiller.exe to run the application, then on Start Scan.
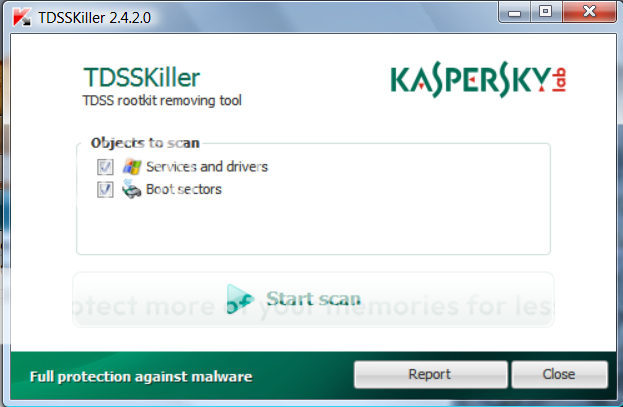
- If an infected file is detected, the default action will be Cure, click on Continue.

- If a suspicious file is detected, the default action will be Skip, click on Continue.

- It may ask you to reboot the computer to complete the process. Click on Reboot Now.

- If no reboot is require, click on Report. A log file should appear. Please copy and paste the contents of that file here.
- If a reboot is required, the report can also be found in your root directory, (usually C:\ folder) in the form of "TDSSKiller.[Version]_[Date]_[Time]_log.txt". Please copy and paste the contents of that file here.
- Under the Custom Scans/Fixes box at the bottom, paste in the following
-
Extras.TxtLockSearch.txtmbam-log-2010-11-09 (20-55-37).txtOTL.Txtscan.txtWVCheck_0730_10-11-2010.txtckfiles.txt
I was not able to run the GMER rootkit scanner, as everytime I tried, my computer would stop working - and I'd have to reboot. Also

malware help
in Malware Removal
Posted
ESETSmartInstaller@High as CAB hook log:
OnlineScanner.ocx - registred OK
# version=7
# IEXPLORE.EXE=8.00.6001.18702 (longhorn_ie8_rtm(wmbla).090308-0339)
# OnlineScanner.ocx=1.0.0.6211
# api_version=3.0.2
# EOSSerial=ced17bc579bdbb4d83ab388588026ff9
# end=finished
# remove_checked=true
# archives_checked=false
# unwanted_checked=true
# unsafe_checked=false
# antistealth_checked=true
# utc_time=2010-11-14 09:26:16
# local_time=2010-11-14 04:26:16 (-0500, Eastern Standard Time)
# country="United States"
# lang=9
# osver=5.1.2600 NT Service Pack 3
# compatibility_mode=512 16777215 100 0 0 0 0 0
# compatibility_mode=3589 16777189 80 100 3186775 25569185 0 0
# compatibility_mode=5889 16764286 0 60 63276073 129583984 0 0
# compatibility_mode=8192 67108863 100 0 0 0 0 0
# scanned=79363
# found=4
# cleaned=4
# scan_time=10347
C:\Program Files\Unlocker\eBay_shortcuts_1016.exe Win32/Adware.ADON application (deleted - quarantined) 00000000000000000000000000000000 C
C:\System Volume Information\_restore{006C6A46-FD8D-46D8-B161-F7C8FE8E6AC5}\RP1044\A0283616.exe Win32/Adware.ADON application (deleted - quarantined) 00000000000000000000000000000000 C
F:\iTunes\iTunes Music\stay young by we the kings HIT TOP50.mp3 a variant of WMA/TrojanDownloader.GetCodec.gen trojan (cleaned - quarantined) 00000000000000000000000000000000 C
F:\My Music\iTunes\iTunes Music\stay young by we the kings HIT TOP50.mp3 a variant of WMA/TrojanDownloader.GetCodec.gen trojan (cleaned - quarantined) 00000000000000000000000000000000 C